[bannerTop]
Welcome to our Sage 2.0 Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC.
The main topic of the article below is the way a virus known as Sage 2.0 Ransomware normally acts. To sum up the nature of this malicious program briefly, we would like to inform you that it is a Ransomware-type program, which is capable of encrypting your most important data. The next action that you can expect from this terrible virus is the popping up of an alert message letting you know that your files have been hijacked and in order to have them back, you are supposed to pay ransom. You can find out more below.
Sage 2.0: The worst cyber nightmare
To be honest, seldom could you come across a virus more malicious than any version of Ransomware. These are the most intrusive and bothering programs on the web. More and more users become infected with them thanks to the more and more flexible distribution methods. Once upon a time, when Ransomware first originated in Russia, the main distribution method was via sending contagious emails containing such malware either in the letter itself or in a contaminated attachment. Nowadays, as Ransomware is on its rise, you can catch a version of it from practically anywhere on the web – the same infected letters, drive-by downloads, shareware, torrents, contagious webpages, malvertising. Please, note, that if Sage 2.0 has come to you from an infected letter from your email, it has most probably entered your system by benefiting from a certain vulnerability and exploiting a Trojan horse virus. Scan your device for Trojans as you never know how exactly this malware has contaminated your machine.
You are already aware of the fact that Sage 2.0 makes some of your files inaccessible. It chooses which ones will be encrypted after it has scanned all of your disks and drives and has concluded which ones exactly you most regularly open or visit or use in another way. Then all these files get enlisted and when the process of encoding begins, the program encrypts all of them one by one. After the entire list of programs is encoded, Sage 2.0 generates a very frightening ransom notification that consists of payment deadlines and other related details.
Can this process be noticed?
In some cases some affected users could perceive the fore coming danger, because they might experience a significant slowdown of their computers and might be wise enough to take a look into their Windows Task Manager. There the program consuming the biggest amounts of resources will be shown at the top of all the processes going on. In case you happen to be one of these users, the best you can do is turn off your PC immediately, close all the network and other connections which may result in spreading this malware and then restrain from turning on your computer again before you have managed to solve the issue. Unfortunately, in most of the recorded cases, the infections don’t get noticed before the encryption of all the targeted files and the popping up of the ransom notification.
Could this process be reversed? Is it possible to decrypt the encrypted data?
This is a very sensitive matter because “yes” and “no” are both correct answers to the above questions. Generally, it is always possible to remove this malware infection. For that purpose we are offering you to follow the instructions in our Removal Guide below. Usually, the Ransomware-type viruses can be removed if you follow the instructions closely. Getting back your encoded data, though, is a completely different story. No Removal Guide, no expert, no software could ever guarantee the safe recovery of your encrypted data. To be completely precise, even paying the requested sum of money may not give you back control over your files. All the possible outcomes depend on the intentions of the hackers, who have programmed Sage 2.0 to encrypt your files. Sadly, you may never be able to access your data again as most commonly, hackers do not have good intentions and are not helpful at all. They are just after your money. Neither the payment of the demanded ransom, nor the removal of the virus might restore your files.
What we suggest that you do
Never risk sending your hard-earned money to any criminals, including the cyber ones. These people are breaking the law and you cannot expect them to be honest and trustworthy. Try all the possible measures against such viruses before you resort to paying the ransom. Consult a specialist, give our Removal Guide below a try, just don’t make the hackers believe their actions could bring them even more money by giving them yours, because it may encourage them to harass other people and blackmail them for their money.
Sage 2.0 Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
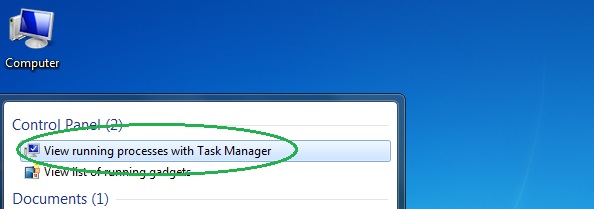
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
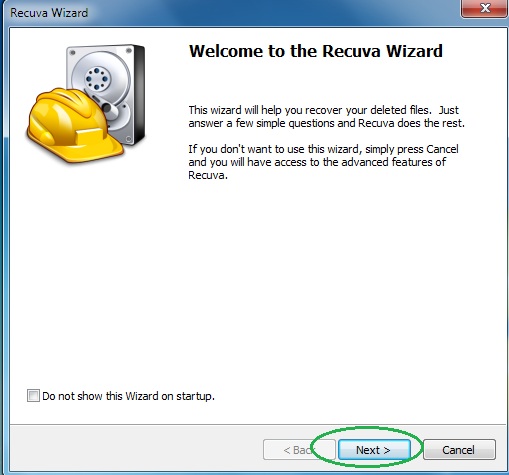
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
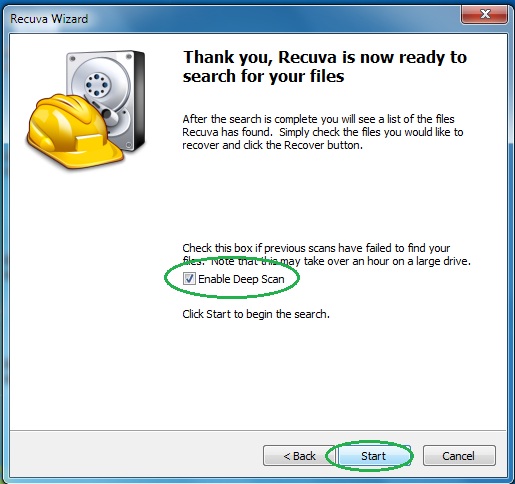
- Wait for the search to finish and then select which of the listed files you want to restore.

