Welcome, reader, to our Playbar.biz removal guide. The following instructions will aid you in removing the unwanted software from your PC.
How Playbar.biz came on your computer without any notice? And why is it flooding you with its ads, pop-ups and banners every time you open your browser? If you are tired of the constant page redirects and new tabs that interrupt your browsing, then here we are going to help you solve this issue once and for all. The reason for your disturbance is known as a browser hijacker and the program you are facing is one of the many. In case you have no idea when and how you downloaded and installed Playbar.biz and if it’s harmful or not, in this guide we are going to explain all its common features and typical behavior, as well as the effective methods to manually remove it from your system. With the help of the removal guide below you will be able to completely clean all remaining files and bring your browser back to normal. And what is more important, you will learn how these types of programs are distributed and how to keep them away the next time you come across them. Just read the next lines to know more.

Where is Playbar.biz coming from?
Browser hijackers are pieces of software, which are used as online advertising tools. They are created with the sole aim to display dozens of ads, banners and pop-ups and this way advertise different products and services directly on the user’s screen. This is the case with Playbar.biz – one of the many programs of this type. It is primly developed with the capability to load the user’s screen with a constant flow of ads, and redirect their searches to sponsored pages and promotional links. It is also capable of changing the search engine with a sponsored one and replacing the homepage with another unknown page. Many advertisers actually pay for such a service to bring traffic to their websites and make people click on the ads. This is a well-known method called Pay-Per-Click, where every click on the ads caches into income and many businesses and programmers profit out of it by developing and distributing browser hijackers.
You have probably heard that today many download websites and programmers, who distribute free software, use the so-called “download clients” or “installers” to monetize the services they provide for free. If you enjoy freeware and often download and install free applications from different web locations: open source download platform, torrents, direct downloads, file sharing sites or spam emails – you may be offered to install additionally promoted piece of software. It often may come in the form of a browser hijacker, ads-generating software, a toolbar or a plug-in that may expose you to advertisements.
To avoid such potentially undesired programs getting installed along the software you install, pay close attention to each step during the installation process. If you simply run the standard setup, you may not see what is bundled in the package. That’s why we advise you to go for the custom/advanced option instead. It will reveal all the additional software which, if not unchecked, may later apply undesired changes to your browser homepage, change your default search engine or expose you to ads.
Is Playbar.biz legit?
Despite that the browser hijackers’ activity may often appear like a nasty virus infection at first sight, these programs do not represent any serious security risk to your system. More often than not, they are wrongly referred to as viruses, mostly due to the deceptive and aggressive advertising techniques they employ. However, security experts do not see any serious security risks in such programs and calling them malicious would be a bit exaggerated compared to some real malware threats like Ransomware, for example. It would be more accurate to call browser hijackers like Playbar.biz potentially unwanted programs – they do not contain malicious scripts, but still their activity may bring some irritation and disturbance to some users, which is the reason why they would rather uninstall them.
How to keep your system away from Playbar.biz and other similar software?
As you probably know, prevention is always better than having to deal with the trouble later, therefore here we will point out some essential prevention tips that every Windows user should know. If you want to keep your system safe from serious malware like Ransomware, or even some harmless but annoying applications like Playbar.biz, here is what you need to know:
- Install reputable antivirus software and keep its virus definitions regularly updated.
- Make it a habit to perform regular system scans.
- If possible, avoid downloading and installing free software from unknown web locations.
- Do not click on ads and randomly generated messages and pop-ups – they are often used by hackers to infect users with Trojans and Ransomware.
- Avoid clicking on spam messages, too-good-to-be-true offers, and instant downloads – you never know what they may hide.
And last, but not least, always check what is in the bundle by clicking the custom option in the setup. This way you may prevent any browser hijacker from getting installed on your system unnoticed.
SUMMARY:
| Name | Playbar.biz |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | A huge amount of ads flood your screen and your homepage and web searches are getting redirected. |
| Distribution Method | Free software usually comes bundled with browser hijackers, but you could also find them on file sharing platforms, download clients and installers. |
How to Remove Playbar.biz
I – Uninstallation
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot Playbar.biz, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
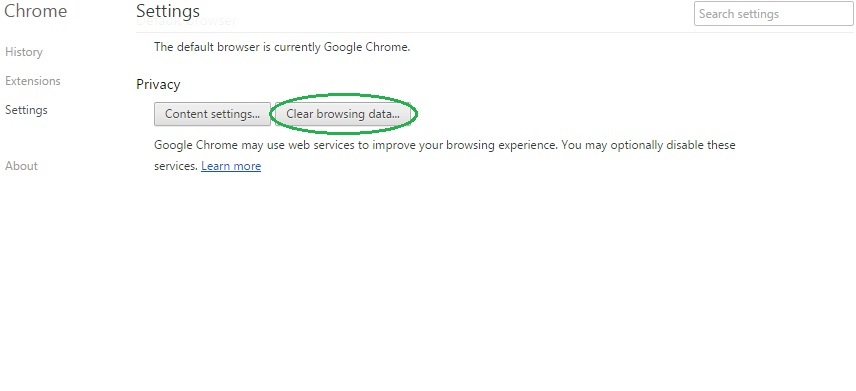
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
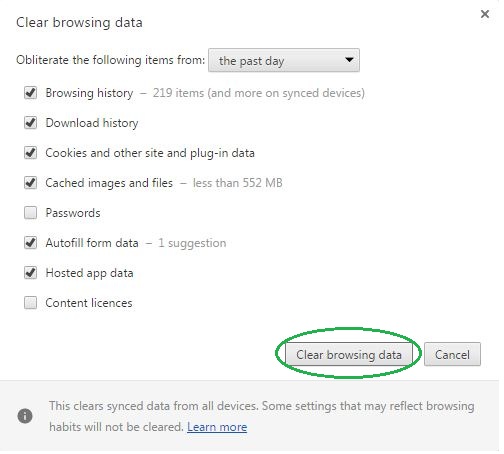
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Playbar.biz on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Playbar.biz might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Playbar.biz, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
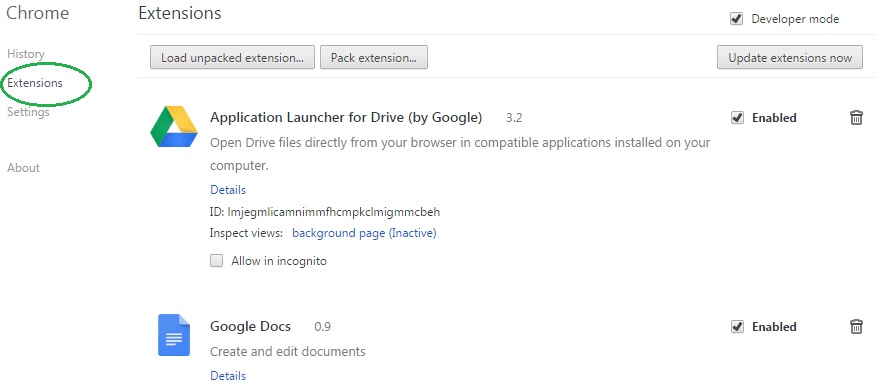
- In the start menu search box write View Network Connections and open the first result.
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
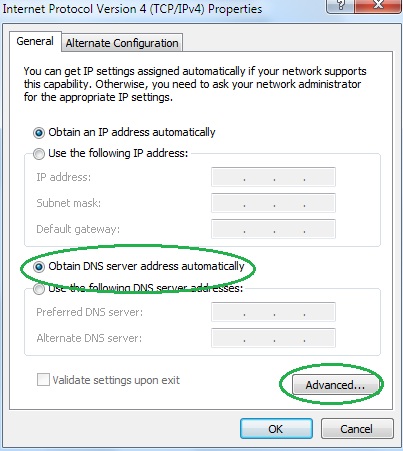
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
