[bannerTop]
Welcome to our PetrWrap removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
Ransomware sounds dreadful enough to even mention it, but what should you do if you have been infected with one? On this page we are going to talk about that, and more precisely, we are going to discuss one particular file-encrypting version, which is called PetrWrap. Unfortunately, this threat is spreading very fast on the web and many users have recently reached us with help requests on how to deal with the nasty Ransomware. For all those in need, who had the “luck” of meeting PetrWrap, here we’ve posted a removal guide, which explains everything – from distribution, infection, and the encryption process to its removal. We’ve put our team to work to help you even restore some of your encrypted files. Unfortunately, we can’t promise you miracles when it comes to the recovery from the Ransomware encryption, but still, giving the instructions below a try may save you a couple of hundred bucks for the ransom payment.
PetrWrap has encrypted your files – what does it mean?
We don’t want to get you panicked, but you are really in trouble in case that Ransomware like PetrWrap has attacked your machine. This type of malicious software is very popular nowadays, mostly because of the effective blackmail scheme it uses. The criminal hackers, who create such harmful scripts, use a special encryption algorithm to lock all the data, found on the infected machine and then ask the victim to pay ransom to unlock it. This is exactly what PetrWrap does to your files – it applies a very complex encryption, which basically prevents you from having access to your files and keeps them hostage until you pay the required amount of money. If you do that, the hackers usually promise to send you a secret decryption key, which can convert the encrypted files back to normal. However, they may charge you a lot of money for the key and the worst is that there is no guarantee that you will really get it.
PetrWrap can infect you without any symptoms.
Ransomware threats are very sophisticated, so you’d better not underestimate their tricky abilities. Infections like PetrWrap are capable of compromising you without you even knowing it. They spread usually in combos with a Trojan horse, which creates security holes in your system, this way allowing the Ransomware to sneak inside undetected. Spam email campaigns, malicious attachments, fake ads, misleading links and sketchy pop-ups may also be transmitters of the infection. All it takes is for you to click on one such seemingly harmless piece of content and you will soon come to know about the harmful results. What is worse is that you may not be able to detect the Ransomware on time and prevent it from encrypting your files. It will reveal itself only after all the files, found on your machine, are secured and you don’t have access to them. Only then, a ransom note will appear on your screen, prompting you to the payment instructions. The hackers, behind PetrWrap, will most probably try to panic you with all possible means. They may set a short deadline for you to make the payment or they may threaten to delete your files or leave them forever locked if you don’t fulfill their demands.
What to do?
Not having access to your own data is indeed a bad feeling. Being ruthlessly blackmailed to regain access to it is even worse. In such a situation, you are more likely to act impulsively and without much rationalization. However, this may be the worst thing you could do. The crooks behind PetrWrap rely on that and they won’t hesitate to manipulate you just to take your money as soon as possible. A very common trick they use is sending just half of the decryption key (a public key) to the victims as an act of good will and promising to send the other half the moment they get the ransom payment. However, the sad statistic shows that they usually disappear the moment they see the money, fooling their victims and leaving them with their files encrypted. You don’t want to be the next fooled one, right? Then you have an option – to remove the Ransomware from your computer and restore some of your files by other means. This can happen if you follow the instructions in the removal guide below. They are detailed enough for you to detect the tricky threat on your machine and manually delete it. Extracting some of the files from system backups is a possibility that the crooks won’t tell you about, but you can try to do that with the help of the steps below. Do you have some file copies on an external drive or a cloud? That’s even better! Once you clean your system from the infection, use them to recover your files and treat yourself a beer. You deserve it.
PetrWrap Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
Preparation: You need to repair the Master Boot Records of your PC. In order to do that you will need the Windows installation CD. Once you put it in your DVD drive, select the boot Windows from CD/DVD option. Once Windows boots from the CD/DVD select Windows Repair. Now you will need to open the Command Prompt. On most Windows OS versions you can do that by typing Command Prompt in the Search Field and clicking on the corresponding action. If you are running on a Windows 10 though, you can do that by opening Start Menu => All apps=>Windows System=> locate Command Prompt. Once you run it you need to do the following:
Type bootrec / fixmbr and hit enter.
Type bootrec / fixboot and hit enter.
Type bootrec / rebuildbcd and hit enter.
You can now reboot your system and proceed with the removal of PetrWrap Ransomware Virus.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
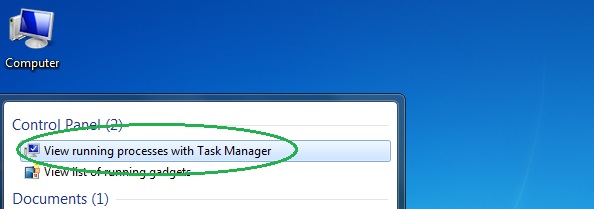
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
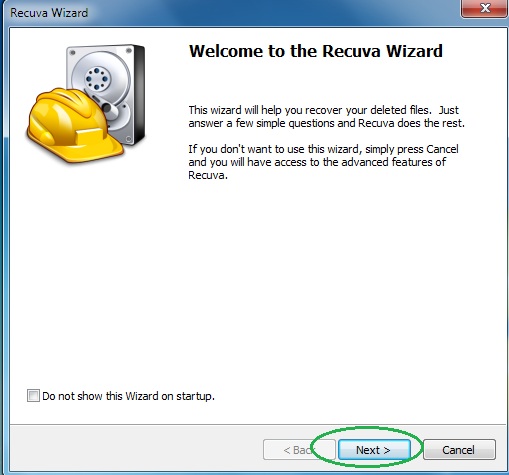
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
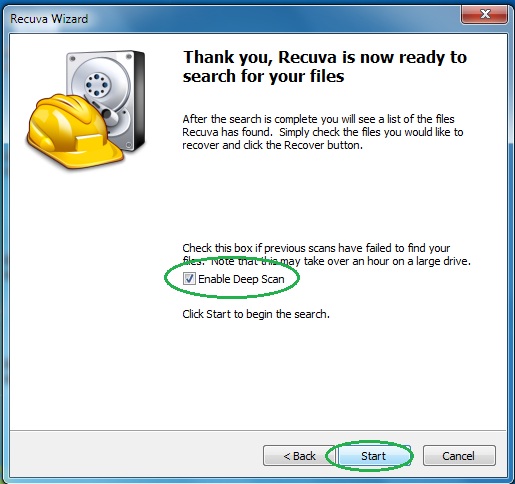
- Wait for the search to finish and then select which of the listed files you want to restore.

