[bannerTop]
Welcome to our Mobilemonetize.me removal guide. The following instructions will aid you in removing the unwanted software from your PC.
No one likes Browser Hijacker programs. They are annoying, obstructive and can even, in certain cases, compromise the security of your computer. Due to this as well as due to the recent release of yet another program of that type called Mobilemonetize.me, we have decided to write this article in order to provide our visitors with more information on what this type of software is all about and how you can successfully deal with a Hijacker program if one has gotten inside your PC.
Some of the most common issues that users seem to be encountering when dealing with a Browser Hijacker is that the pesky program tends to introduce unwanted and irritating alterations to the browsers that are on the PC (Chrome, Firefox, Edge, etc.). For example, such a program could change the homepage or replace the previous search engine of the browser as well as install new toolbars that nobody really wants. To add to that, many Hijackers have the unpleasant tendency to generate and trigger intrusive and obstructive web-ads and page redirects, which drastically decreases the quality of one’s online experience and might also expose the computer to different security hazards (more on that later). In case you are presently struggling with a program like Mobilemonetize.me that seems to possess those unpleasant traits, we advise you to take a look at our Browser Hijacker removal guide and use it to uninstall the nagging piece of software once you’ve finished reading the main section of the article.
What is the actual purpose of a Browser Hijacker program?
For starters, we ought to tell you that Hijackers aren’t some sort of noxious and malicious viruses. The real threats that you should be concerned with are malware types the likes of Trojans and Ransomware. A typical Hijacker, on the other hand, shouldn’t pose a direct threat to the security and safety of your computer system or personal files. The primary purpose of most Hijackers isn’t to harm your computer. Instead, the majority of programs that belong to this category are mainly used for internet marketing and advertising. Surely, the methods they usually employ are quite unpleasant and irritating but this is not to say that a Hijacker would try to damage the system of your PC or steal or corrupt your private data that’s stored on the computer’s hard drive. However, it is also important to note that most Hijacker programs do not really provide the user with any real useful function, trait or feature that would make keeping the program on the computer worth it. Because of this, and also, because at times Hijackers might still hold certain security risks, we believe that it is best if you simply take the necessary measures to wholly remove the unwanted software from your machine. As we already mentioned, we can assist you in doing that with our guide for removing Hijackers.
Security risks
While Hijackers aren’t as dangerous or as malicious as Trojan рorses or Ransomware viruses, some of these programs might still potentially lead to the exposure of your PC to a variety of online threats – something you must prevent at all costs. Normally, it is advisable that you do not use the new toolbar or search engine that Mobilemonetize.me could have added to your browser since those might not always be safe. Also, if you see that the Hijacker is trying to spam your browser with intrusive ads and page redirects, be sure to avoid any interaction with whatever gets generated by the nagging program. You never know if you aren’t going to get redirected to some shady and unreliable webpage should you click on anything displayed by the Browser Hijacker, which is why it is simply better to not do that. All in all, if you think that there is an application on your PC which belongs to this category, the only thing that you should do with regards to it is see to its removal.
How to ensure that the Hijacker does not return
Even though keeping one’s PC safe is fairly easy to do, many users seem to forget about some of the essentials that would allow them to do that. Do not be one of those users and make sure that you always use your common sense when going online. What this means is you must always stay away from sites that might be illegal and potentially harmful and not interact with any messages/e-mails that could be potential spam. Additionally, do not install any new programs before you have made certain that there aren’t any optional installs which could be potentially unwanted. If you see that there are any applications bundled to a program you want to install that look unreliable, be sure to uncheck them before moving on with the installation of the main piece of software.
Mobilemonetize.me Removal
I – Safe mode and revealing hidden files
II – Uninstallation
[bannerMiddle]
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
If you are unable to spot Mobilemonetize.me, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
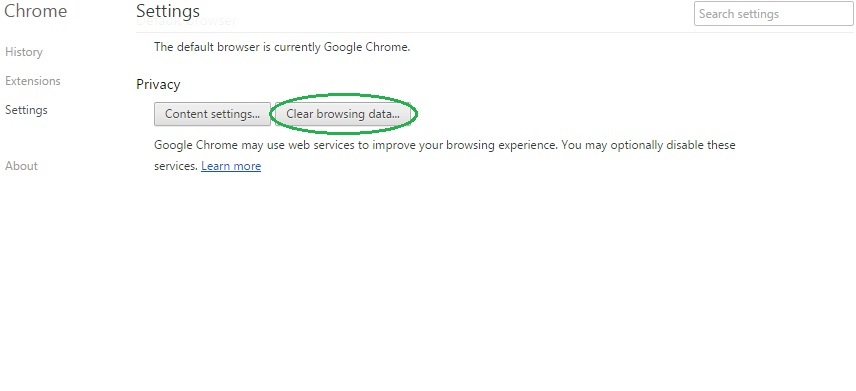
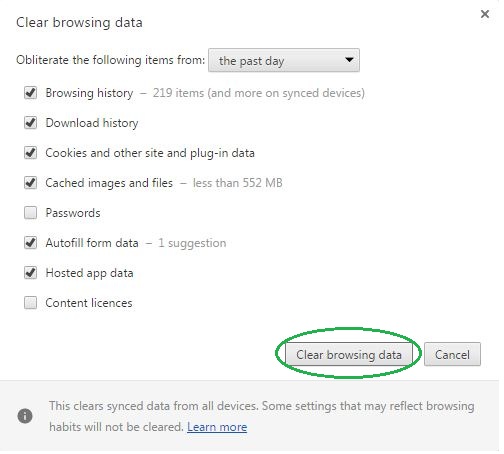
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
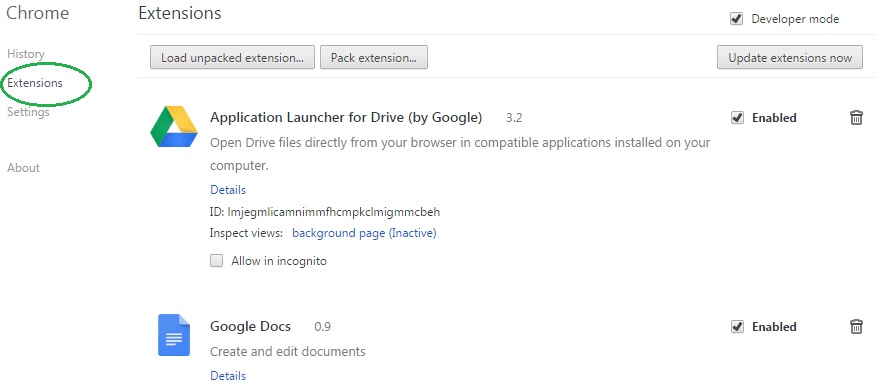
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Mobilemonetize.me on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Mobilemonetize.me might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Mobilemonetize.me, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
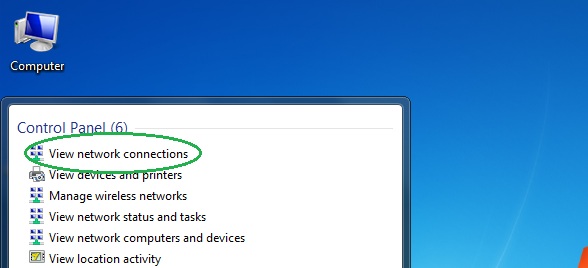
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
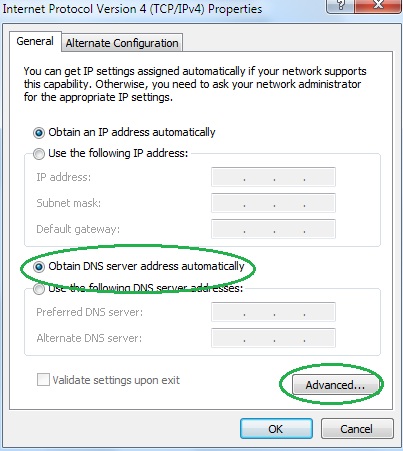
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
