[bannerTop]
Welcome to our .Jaff Virus Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
If it’s accurate to proclaim any piece of software as particularly dangerous and very hard, sometimes impossible to remove or fight, this program is going to be a representative of the Ransomware category for sure. The exact version of the ransom-requiring software family, which we will be discussing here, is .Jaff Virus Ransomware. Normally, this program can sneak into your device without giving any signs for that and without the need to receive neither your informed, nor your uninformed approval. After that, an encryption process begins, as a result of which all the files the program has marked as essential to you become its victims. Later on, a ransom is demanded via an alert notification that appears on your display. All the other characteristic features and effects of this malware will be thoroughly explained in the paragraphs you are about to read.

Ransomware can be described as a software type that does something incredibly harmful to any of your devices, and on completion of this awful mission demands a ransom to undo its harmful activities. There are various versions of ransom-requiring viruses, which may harm your PC or a different device in diverse ways. You can review them in the following paragraphs.
Popular Ransomware Subcategories:
The main types of ransom-requiring software we know about today are the ones mentioned here:
- FILE-ENCRYPTING RANSOMWARE VIRUSES:
This is the most famous and numerous subgroup of Ransomware. .Jaff Virus Ransomware is an exemplary member of this kind of Ransomware exactly. What such viruses normally do is they infiltrate your system (which may happen via exploiting a Trojan horse virus or automatically after you have come across one of its common sources). Later on, they will go on to scan all your hard drives for the most regularly modified/accessed data. Then, these viruses will be ready to perform the encryption process and will use a double key, consisting of two parts – a public and a private one, for this purpose. After the completion of the data encoding, you normally receive a full-screen ransom-requiring message, consisting of some payment details and sometimes even threats. - SCREEN-LOCK RANSOMWARE VIRUSES:
The programs from this subcategory can also infiltrate PCs like the ones from the file-encrypting subgroup. The difference is that no file encoding occurs. Instead, only your monitor is rendered inaccessible, as a full screen banner is generated and you are made unable to access any icons on your desktop. After that you are required to pay a ransom in exchange for removing this blocking message. - MOBILE-ENCRYPTING RANSOMWARE-BASED PROGRAMS:
The viruses from this subgroup can only infect mobile devices and act in a way, which is similar to that of the aforementioned category – the screen-locking one. Once more, your entire mobile device display gets blocked by the produced ransom-demanding notification and you need to pay a ransom for your device’s display decryption.
Most of the infections which result from .Jaff Virus Ransomware normally happen when:
In fact, there may be many different means of spreading such viruses. Below we will only mention the most widely spread ones:
- The process famous as malvertising: this malicious program may get distributed via fake contaminated advertisements in various forms that can pop up online. Immediately after you click on such a pop-up, the infection occurs automatically.
- The spam emails you get on a daily basis: Ransomware might or might not be be bundled with a Trojan horse virus and spread in a spam email or any of its corresponding attachments. As soon as you download/open such strange attachments or letters or follow a link in that email, you will end up getting infected.
- On all kinds of contagious webpages like torrent sites, files-sharing pages, as well as video and audio-streaming ones.
Is it possible to counteract such a threat in any way?
To our mutual disappointment, there aren’t really any solutions, flexible and functional enough to both get rid of the virus and decrypt your encrypted files in 100% of the cases. No matter what you do, you are going to risk your encoded files and the future of your entire system. That’s why we suggest that you should not pay the hackers, who are bothering you with threats in the first place. Make sure to first try other methods:
- Don’t waste time and pay a visit to a specialist with some experience with such an issue;
- Order a special version of software to try to solve the issue with your locked-up data.
- Stick to the instructions inside a Removal Guide, designed by experts. We have attached such a Guide here for you to use for free.
- If nothing of the above can help you, proceed with paying the ransom, however, bear in mind that no guarantee is given for the restoration of your files even if you do so.
Always remember that the only thing that successfully deals with Ransomware-like viruses is the process of regular file back-up. If you do that regularly, no threats will bother you because you will have more copies of all the data that you consider vital.
SUMMARY:
| Name | .Jaff |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Not many in number and most of the time they are completely unnoticeable, until the ransom notification is generated. |
| Distribution Method | From malicious ads and fake system messages to spam; various emails and contaminated websites. |
.Jaff Virus Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
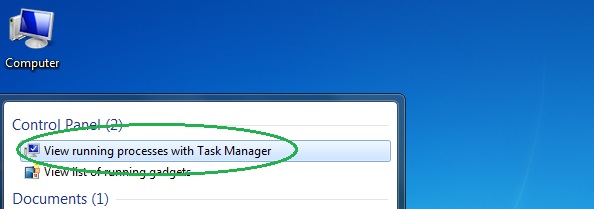
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
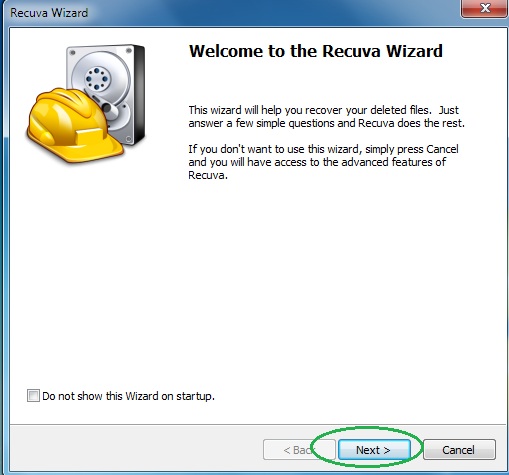
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
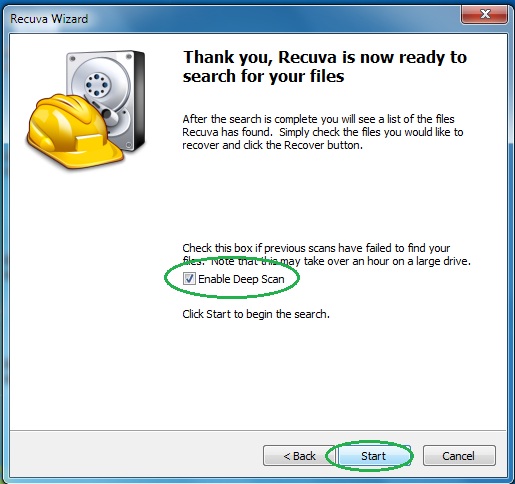
- Wait for the search to finish and then select which of the listed files you want to restore.