[bannerTop]
Welcome to our Gebdp3k7bolalnd4.onion Ransomware Virus removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
In this article, our readers will be provided with all the basic information about one very harmful cryptovirus called Gebdp3k7bolalnd4.onion Ransomware Virus. This cryptovirus is a typical example of file-encrypting Ransomware, and as one of the latest of its kind, it comes with a pack of malicious abilities. Detecting it is very difficult, and once it attacks your computer, it applies a special encryption algorithm to all the files, found on the hard drives. This way, it locks them and keeps them hostage until a certain amount of money is paid as ransom. A disturbing ransom notification usually discloses the harmful consequences, and there, the hackers, who stand behind the Ransomware, place their demands and deadlines. The victims are threatened not to be able to access the encrypted data ever again unless they pay the requested amount of money. If they pay, however, the criminals promise to send them a special decryption key, which can reverse the malicious encryption and bring the files back to normal. How can one handle such a nasty blackmail scheme is what we are going to cover in the next paragraphs, so, if you are one of the unfortunate victims of Gebdp3k7bolalnd4.onion Ransomware Virus, make sure you read the information that follows and take a look at the Removal guide at the end of the page.
How can Gebdp3k7bolalnd4.onion Ransomware Virus infect you?
Ransomware viruses are one of the most problematic types of malware. They can infect you in a number of ways and just one click on an infected transmitter is enough for that. Threats like Gebdp3k7bolalnd4.onion Ransomware Virus can be found on some shady websites, where sketchy ads, spam messages, and pop-ups prompt you to click or download something. Torrents, free installers from non-trusted developers, emails and different attachments can also contain such infections. In most of the cases, a Trojan horse delivers the Ransomware inside the computer thanks to some system vulnerabilities and exploit kits. Usually, at the moment of contamination and even during the attack, there are no signs that could give the Ransomware away. Most of the antivirus programs also turn out to be ineffective when it comes down to detecting the malicious encryption process, which makes spotting the cryptovirus on time very hard.
How does Ransomware work?
A Ransomware attack will never harm directly anything on your PC. It won’t destroy your files, it won’t corrupt your software and won’t even try to mess up with your OS. This malware works quite differently, compared to some other types of PC threats like Trojans or typical viruses, which usually cause certain system malfunction or corruption. It uses a method known as file encryption, which is generally non-malicious method when used to secure your data from unauthorized access. But when implemented in a criminal scheme, this same file encryption can be used for blackmail purposes and prevent you from accessing your files unless you fulfill the demands of the hackers. Gebdp3k7bolalnd4.onion Ransomware Virus is a threat, which uses such encryption for the nasty blackmailing of its victims, but in the next lines, we are going to tell you how to remove and counteract it.
The ransom payment and the options…
If you have to deal with an infection like Gebdp3k7bolalnd4.onion Ransomware Virus, you have to know a few basic things. The hackers, who control the Ransomware, rely on your fear, lack of information and impulsive decisions in order to extort money from you. That’s why it is very important for you not to act like a victim and to inform yourself about all the possible options of counteracting the blackmail scheme and removing the infection. An alternative that we can offer you is to use the instructions in the removal guide below. They can save your machine from the cryptovirus. Once you remove the infection, you can start with your attempts to recover some of your encrypted data. We have included some instructions on that as well, and some users have found them helpful. You can give them a try, or you can use your own data backups, if you keep any, and get back some of your files. Unfortunately, so far there is no solution that can promise you a 100% recovery from the attack of Gebdp3k7bolalnd4.onion Ransomware Virus. However, paying the ransom to the crooks is the least advisable course of action. Not only can the amount of money, asked by the hackers, be huge, but you have absolutely no guarantee that they will really send you the decryption key you are paying for. And what if it doesn’t work properly? You will not be able to get neither your files, nor your money back and even the authorities may not be able to help you because, in most of the cases, the ransom is requested in Bitcoins. This is a special untraceable cryptocurrency, which helps the criminals remain hidden from the police. So, a much smarter option is not to fall into the trap of the ransom payment and try other alternatives.
SUMMARY:
| Name | Gebdp3k7bolalnd4.onion |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
Gebdp3k7bolalnd4.onion Ransomware Virus Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
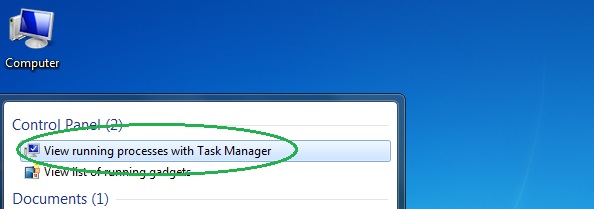
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
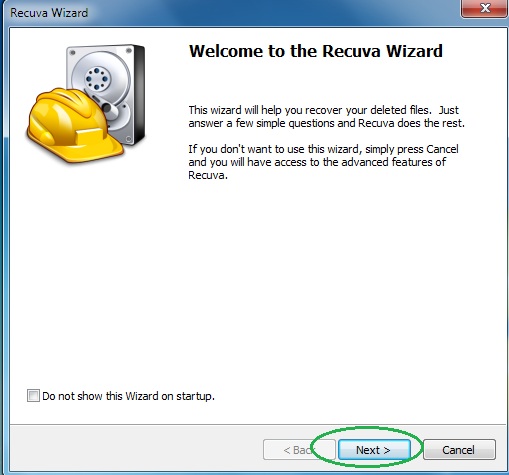
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
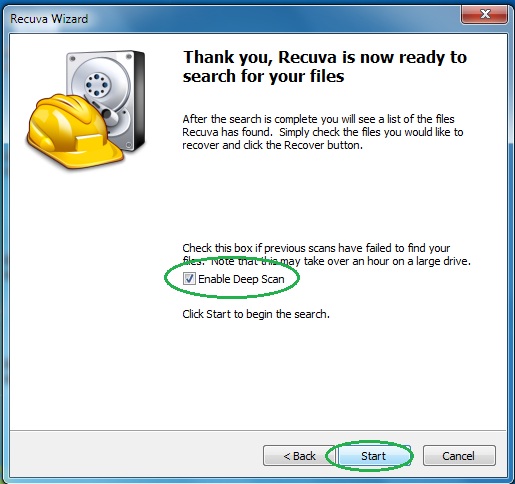
- Wait for the search to finish and then select which of the listed files you want to restore.

