[bannerTop]
Welcome to our Apusx.com “Malware” removal guide. The following instructions will aid you in removing the unwanted software from your PC.
Apusx.com is a program that usually claims to provide its users with a better browsing experience and free functionality. However, security specialists have noticed that it has the characteristics of a potentially unwanted application or more precisely, a browser hijacker. Once installed on your device, Apusx.com may not only change your browser settings but also may show tons of ads. What we have in mind here is the possible change of the browser’s homepage or search engine, the installation of some new toolbar or the unstoppable generation of various aggressive ads, pop-ups, banners and promotional links. In case that your Chrome, Firefox or Internet Explorer has recently been invaded by this program, in the lines below, we have published a free removal guide with precise instructions on how to remove the annoying changes and uninstall all the new components. You can also find a trusted professional removal tool at your disposal, as well as some useful information on prevention and protection from browser hijackers. We encourage you to read the following paragraphs, as they will give you a better idea of the typical features of this type of software and the best and safest ways to remove it from your system.

A first encounter with a browser hijacker – what should you know?
Although we do not claim that browser hijackers are as dangerous as Trojan horses or Ransomware viruses, we must warn our readers that these pieces of software may modify the computer settings after the installation. In most of the cases, the modifications are related to changes in the default search engine and the establishment of a new homepage in the default browser without requesting the user’s permission. As a result of these changes, the affected browser usually starts to redirect the web searches to some predefined websites and to generate tens of intrusive ads, pop-ups, and banners. Such activity is usually seen by the users as very invasive, however, according to the law, this is just an aggressive online advertising approach. It is typical for the browser hijackers to be related to certain pay-per-click advertising campaigns and to try to expose the web users to specific sponsored ads or websites with the idea to make them click on the suggested content.
It seems that Apusx.com is a program that operates in a similar way since a lot of users have recently contacted our team, reporting frequent redirecting activity. Some people are irritated by the increased amount of online ads they are exposed to, while others have reported that they are being constantly redirected to commercial or strange webpages. Dealing with such activity for the first time may be a bit frustrating, especially if you are not really sure what such software may do.
Generally, security experts do not see a serious system threat in pieces like this, because unlike real viruses such as Ransomware, Trojans, and Spyware, they do not contain malicious coding. However, despite not being malicious, it is not advisable to trust a browser hijacker. Researchers have noticed that some of the ads and links that may get generated by such software may be linked to fake ad campaigns or lead to some phishing web pages. That’s why it is advisable to avoid clicking on the suggested pop-ups and ads, generated by a program like Apusx.com, and uninstall the unwanted browser changes. We already mentioned that you can remove the hijacker manually with the help of the removal guide, but you can also do this automatically with a professional removal tool, which is available at the end of this page.
How can unwanted programs like Apusx.com get into your system?
Many programs like Apusx.com may be advertised through their official web page as software that helps computer users enhance their browsing experience or provide them with some free functionality. Still, it has also been found that a potentially unwanted program may be bundled with other programs or misleading pop-up ads. For instance, the most probable way for a piece like Apusx.com to become part of your computer is through a program bundle installer, which usually contains another software as main. The installation normally happens with your indirect permission the moment you run the bundled software setup and agree to the EULA at once. To avoid such automatic installation, here is what you should do:
- Avoid downloading free software from unknown third party web pages and free download links;
- Select Advanced / User settings instead of Standard / Recommended settings when installing new software;
- Remove the bookmarks of any “extra downloads”;
- Read the official documents such as the End User License Agreement, Terms of Service or Privacy Policy before clicking “I Agree”.
Apusx.com Removal
I – Safe mode and revealing hidden files
II – Uninstallation
[bannerMiddle]
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
If you are unable to spot Apusx.com, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
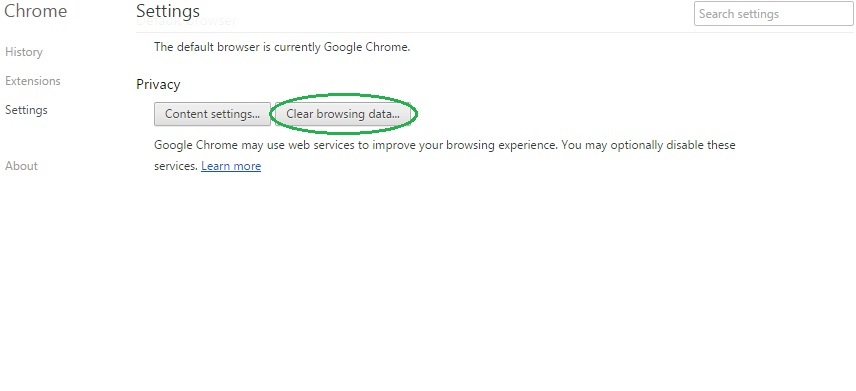
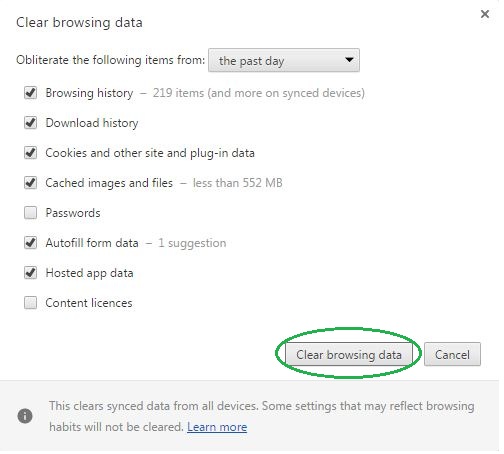
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
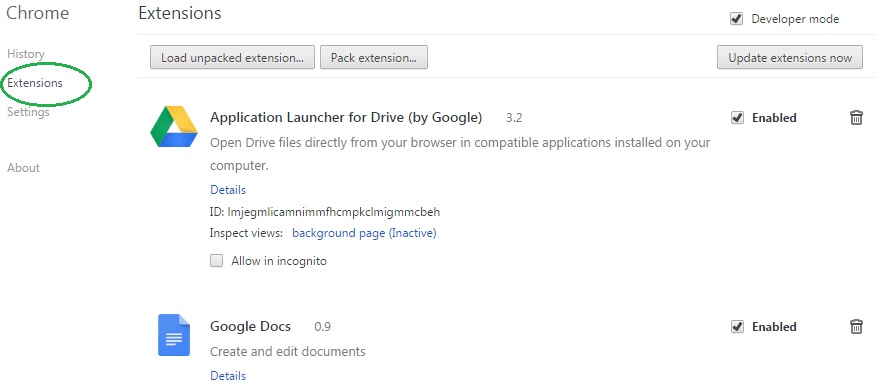
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Apusx.com on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Apusx.com might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Apusx.com, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
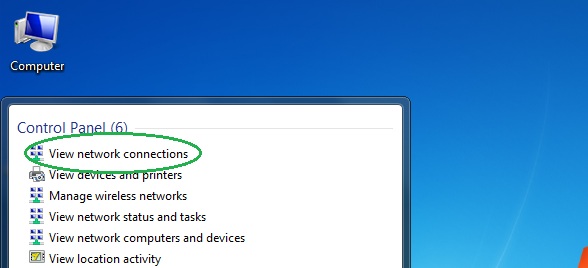
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
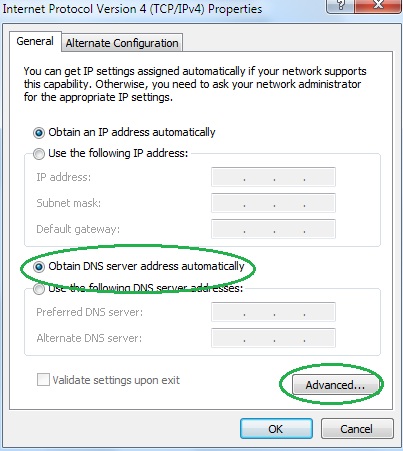
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
