[bannerTop]
Welcome to our Allcry Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
This article describes a really dangerous virus – Allcry Ransomware. It is in the category of the Ransomware which is a kind of malware, responsible for the encrypting of your recently and/or commonly used files, also for blackmailing you for money later, after the actual encryption has taken place. For real, threats like these are perhaps the most hazardous ones you could encounter in the cyber world.
What makes Ransomware-based viruses so horribly terrifying?
Ransomware (the malware group) includes various noxious viruses, and all of them are really tough to remove or deal with. Indeed, even people who have been in the security software industry for years might find it terribly difficult to deal with mischievous programs like these. Essentially, you can find different kinds of Ransomware-based viruses with other ways of operating. The similar feature of all of them is that they are usually programmed to demand a ransom in return for undoing whatever wrong they have done. The paragraph below will give you a better point of view into every version of Ransomware.
Ransomware is divided into the following subgroups:
- The program which is described in detail in this article, Allcry Ransomware, belongs to the file-encrypting subtype of Ransomware. As you have already gotten to know, these programs make files inaccessible to the affected user by blocking them with a complex encryption key. It is very scary to understand that the threats in the notification that appears on your monitor after the file-encryption process are actually true and the files mentioned as encoded really can’t be accessed. Hackers then want you to think that there is only one way of getting your data back and it is to send them the ransom, and they inform you about that with a threatening notification.
- There is also screen-locking Ransomware: such products are designed to lock your monitor by covering it with a huge ransom-requesting alert and making you unable to use any of your PC’s programs and features. Once again, you are asked to pay a certain amount of money if you want your monitor unlocked, and to be again able to access your PC’s capabilities and the programs installed on it.
- Do not think that mobile devices are safe. You might catch the mobile version of these viruses on your smartphone or tablet. This type of Ransomware, as in the case with the desktop-sealing subtype, makes the screen of your device really useless to you by putting a big alert on it. All in all, the plan is the same – you are notified that you will never again access your device if you don’t send the needed money.
- You can, as well, use Ransomware to make cyber criminals pay for their illegal activities. For instance, a lot of national security and intelligence agencies use viruses with the same code to convince some hackers to pay for their criminal activities, or to make their systems unavailable to them and stop their disastrous plans.
Possible sources of Ransomware
Mischievous programs like these could be found in so many different places on the Internet. There isn’t anything safe on the web. On the other hand, if we look at the reports for the recorded infections, most of them have happened when a user has clicked on a fake pop-up. Also, another major cause for an infection could be opening a spam email and its attachments. In the first case your device gets infected automatically and the virus comes as a drive-by download. In the second common case, Allcry Ransomware could be aided by a Trojan horse and these two horrible mates could be hiding in a distrustful email/attachment together. Soon after you start reading a letter like this, the Trojan exploits any existing weakness of your system and sneaks the Ransomware inside it. Clearly, other possible sources exist like torrents, contagious websites and shareware. To be absolutely honest, Ransomware could be carried by anything on social media webpages as well.
The actual infection process takes place in the following way:
The real contamination process happens like this: it does not matter how exactly you have bumped into the virus. Right after Allcry Ransomware is in your system, it has full access to everything. First of all, the mischievous program completes a full scan of the corresponding drivers, trying to define which files are useful and important to you. After that, all of the targeted data that corresponds to that description becomes a victim of encrypting with a sophisticated double-part key. In the end, a horrible notification appears on the monitor of your PC. Thus, you get informed about the fate of your files.
What should be done in case of contamination?
We are really sorry to say, but no solution is universally effective against Ransomware. The removal of the virus, though essential, isn’t all it takes to solve the problem, as the files will still remain encrypted even after that. There are additional measures you will need to undertake, in order to recvevr them. We advise you NOT to pay the wanted money, and to first try to fight Allcry Ransomware on your own. The Removal Guide below is just for cases like yours. We cannot promise you that it will decrypt your files, but in any case this is a sensible way to try to neutralize this cyber threat.
Allcry Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
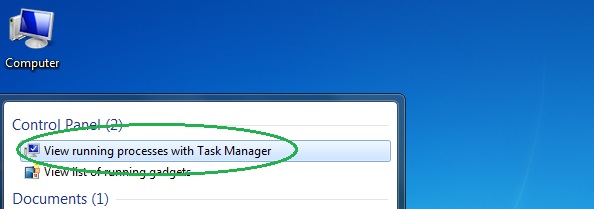
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
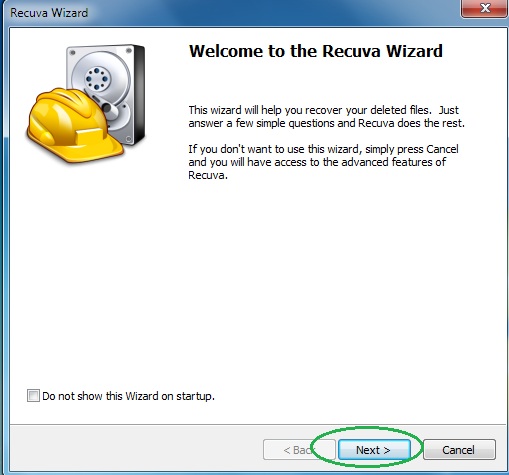
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
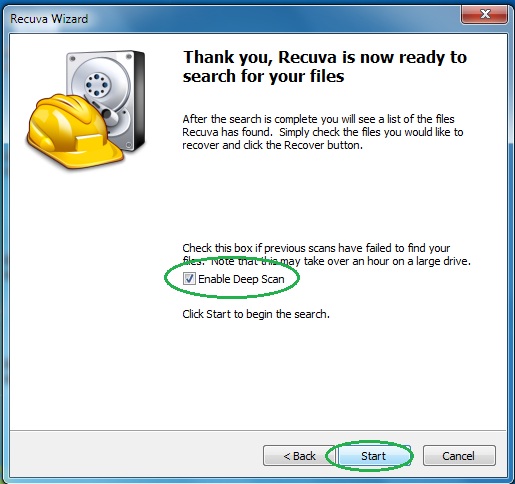
- Wait for the search to finish and then select which of the listed files you want to restore.

