[bannerTop]
Welcome to our Reyptson Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
The newly discovered Reyptson Ransomware Ransomware has recently attacked numerous computers and has caused problems to a lot of online users. Some of the victims of this notorious threat have reached our “How to remove” team with a call for help on how to deal with this brand new infection and its malicious consequences. Unfortunately, the attack of Reyptson Ransomware can be really harmful if you don’t have a full backup of all of your files, because it acts as a cryptovirus that applies a secret encryption to all the data that you keep on your machine. Basically, the encrypting virus usually attaches some unfamiliar extensions to the targeted files and this way makes them impossible to open or use with any program. From then on, the malware operates as a blackmail tool that asks the victims to pay ransom if they want to be able to use their files again. Reyptson Ransomware may also make changes to the Windows registry, which may allow the virus to automatically start every time the computer is booted and encrypt other connected devices or restored files.
Unfortunately, the encryption algorithm, used by this Ransomware is not that easily breakable and there are very few options that may help the victims to recover from its attack. In the next lines, we did our best to research and provide you with some free file restoration instructions as well as a detailed removal guide that can help you remove the infection from your system. However, keep in mind that removing Reyptson Ransomware may not help you get all of your files back. The hackers, who control the infection, will prompt you to purchase a decryption key to retrieve the important documents, photos, audio and video files that have been affected, but most of the reputed security experts, including our team, would encourage you to do something else. Keep on reading to find out more.
The hackers will ask you to pay ransom, but you should carefully research your options!
Ransomware is typically a very tricky threat that can sneak inside your computer undetected and can ruthlessly blackmail you for the access to your own data with the sole aim to make money for its criminal creators. The typical types of files that can be affected by Ransomware like Reyptson Ransomware may include some of the following extensions:
.txt, .doc, .docx, .xls, .xlsx, .pdf, .pps, .ppt, .pptx, .odt, .gif, .jpg, .png, .db, .csv, .sql, .mdb .sm.php, .asp, .aspx, .html, .xml, .psd, .frm, .myd, .myi, .dbf, .mp3, .mp4, .avi, .mov, .mpg, .rm, .wmv, .m4a, .mpa, .wav, .sav, .gam, .log, .ged, .msg, .myo, .tax, .ynab, .ifx, .ofx, .qfx, .qif, .qdf ,.ncf, .nsf, .ntf, .lwp.
However, there might be even more file types that may get encrypted. Usually, the hackers aim for the most commonly used files in order to prevent the victims from using their most needed and favorite data and make them pay as soon as possible to regain their access. Once the encryption is complete, the Ransomware generates a ransom note with exact instructions about the payment and the deadlines.
The requested ransom may vary from a few bucks to a couple of thousands; but even if it is not huge, we do not recommend paying it. If you do not have a backup from where you can recover your files, the options for the recovery of the affected files may not be many; however, the ransom payment may also not bring you the desired restoration of your data. First of all, you cannot be sure that the hackers will provide the promised decryption key for the files. What if they send you another virus instead of a decryption solution? Or what if they simply disappear when they receive the ransom payment? There is absolutely nothing you can do except to hope that they will be good enough to fulfill their promise.
The leading security experts in the field of Ransomware counteraction strongly advise all the victims not to give their money to the hackers because such actions will only not guarantee the recovery of the encrypted data, but will also directly motivate the crooks to develop more infections of this type in the future. What we can suggest you is to remove Reyptson Ransomware and invest this money in reliable PC protection or data backup solutions to keep you safe from future cyber attacks. To eliminate the virus, you can use the manual instructions in the guide below or scan the system with the professional Reyptson Ransomware removal tool. You can also give our file-restoration suggestions a try or contact a professional of your choice for additional assistance.
Reyptson Ransomware Virus Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
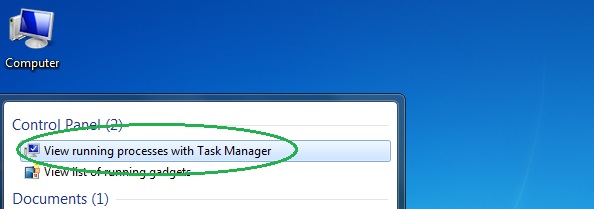
- Open the Start Menu and in the search field type Task Manager.
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
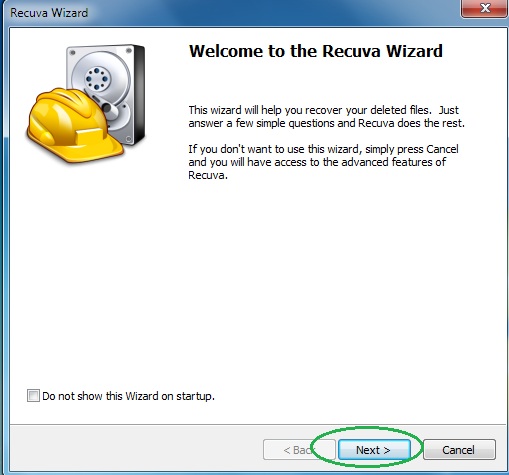
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

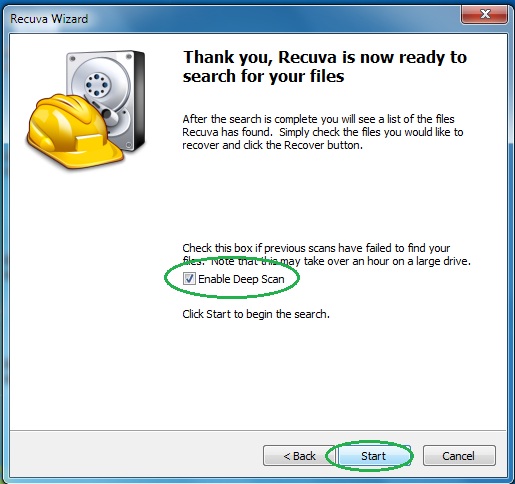
- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
- Wait for the search to finish and then select which of the listed files you want to restore.

