Welcome, reader, to our StartFenster.de removal guide. The following instructions will aid you in removing the unwanted software from your PC.
Maybe you are looking for some details about the program that has currently been making your Chrome or Firefox browser generate a considerable number of banners, boxes, pop-ups and other ads; as well as sometimes redirect you to web pages you cannot recognize; and/or even display a different browser homepage and search engine from the ones you have set. This article strives to give you as much information as possible about the program causing all this annoyance – StartFenster.de.
All you need to know about StartFenster.de
The term “browser hijacker” perfectly describes StartFenster.de. Hijackers are experts in the aforementioned activities and they may affect all popular browsers – Chrome, Opera, Explorer, Firefox, etc. Some users might perceive the changes in their browsers as irritating and even intrusive. The number of displayed ads may annoy the affected users even further. However, there is no concrete reason to worry, as StartFenster.de doesn’t belong to any virus group. It is not a relative of Ransomware – it cannot encrypt any files and make them inaccessible to you. Its actions do not define it as a Trojan, as it cannot use any system/program vulnerability to enter your computer. There is nothing malicious about StartFenster.de, still, it might have some pretty disturbing possible effects. Such is its capability to trace your search requests using your browser history and set the appearance of only advertisements that contain a service, a product or something that you have shown some interest in. Also, this browser hijacker owes its relatively negative image to the redirections it may become the reason for. There have been implications that these redirects actually lead to websites contaminated with viruses, however, these cases are quite rare.
Another possible cause for concern might also be the way StartFenster.de could get into your PC. In fact, there are many possible ways of contamination – spam emails, text documents, redirecting hyperlinks, infected websites and torrent and shareware pages. The most widely used one remains the process of program bundling. This is a very popular practice among developers, in which they mix different types of software like Adware, original programs and/or hijackers like StartFenster.de. It is completely normal and legal, the programmers actually get paid for spreading ad-producing software. Through StartFenster.de and the other programs like it a lot of diverse ads get produced and each of them generates profit for the developers. They also may get paid for setting your browser to redirect you to different websites by using browser hijackers.
If we talk about the way your PC has caught the StartFenster.de infection technically, not in terms of sources, we must mention that many users may believe that this hijacker is capable of self-integrating into your browser. However, this is NOT true. You could end up infected only if you allow it to be installed on your computer, which may happen with your direct or indirect permission. Usually, users are eager to use a piece of software from the aforementioned program bundles and they want to get them installed as soon as they have been downloaded. However, this is a big mistake, as installing any program by choosing the QUICK / BRIEF / AUTOMATIC function of the installation wizard can only let all the programs inside the bundle enter your machine. The right way of putting a piece of software into your system is by installing it via the CUSTOM function of the wizard, as this feature lets you choose what exactly you need/ want from the bundle and what could be neglected. This installation manner will prevent your PC from catching ad-producing software and even malware like Trojans and Ransomware.
What to do in case of an ongoing infection with StartFenster.de
The first step ahead of you is the removal of this hijacker. This may be achieved by following the uninstallation instructions in the guide below. They are very detailed and strive to help you with the important task of freeing your computer from the irritating redirects, ads and the annoying unfamiliar homepage. After you have managed to remove StartFenster.de, all you should focus on is preventing future ad-related issues. This is an achievable goal if you learn the right installation manner and always implement it (as explained above). Also, you should make sure that your system benefits from a functional anti-virus program, Firewall and pop-up blocker. They may not stop all the ads or the infection itself, but they will certainly inform you about possible sources of ad-generating software or block them instantly.
SUMMARY:
| Name | StartFenster.de |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Many annoying signs like redirects, pop-up and banner ads, as well as a newly-set browser homepage. |
| Distribution Method | Via program bundling – inside a software combo with other software; in spam emails; contaminated hyperlinks, websites, documents, attachments, torrents. |
StartFenster.de Removal
I – Uninstallation
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot StartFenster.de, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
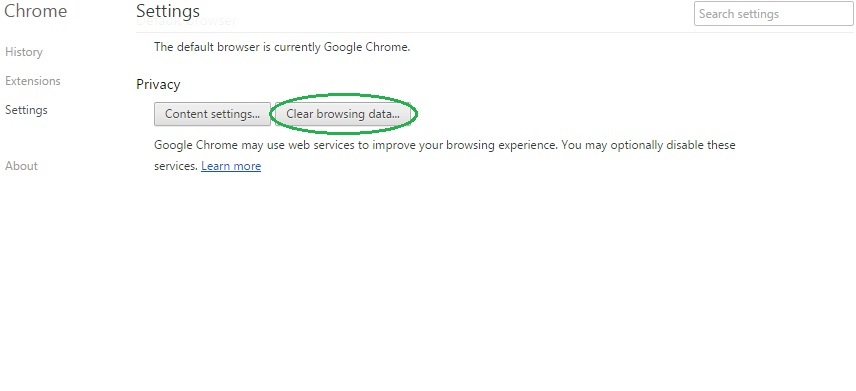
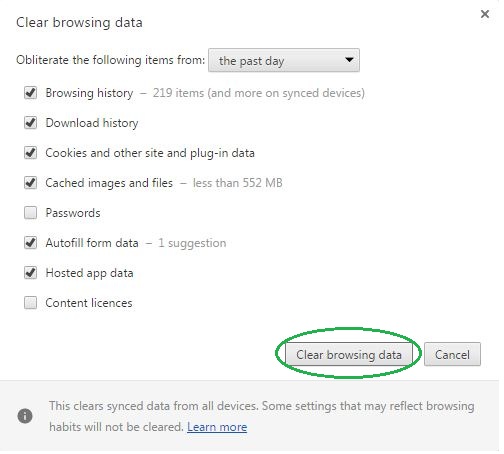
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
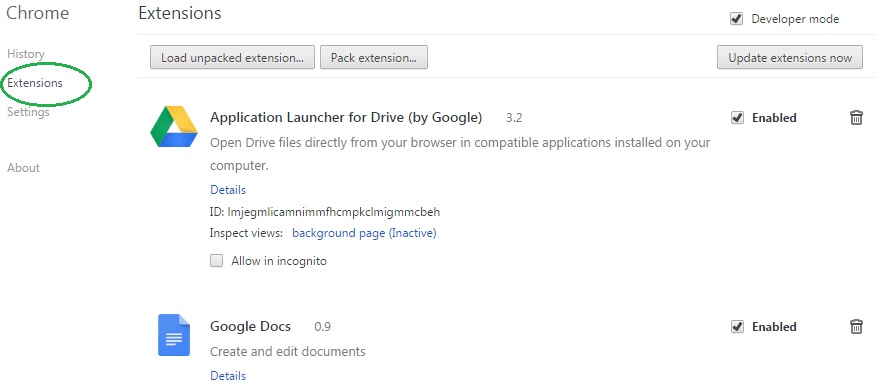
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name StartFenster.de on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name StartFenster.de might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by StartFenster.de, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
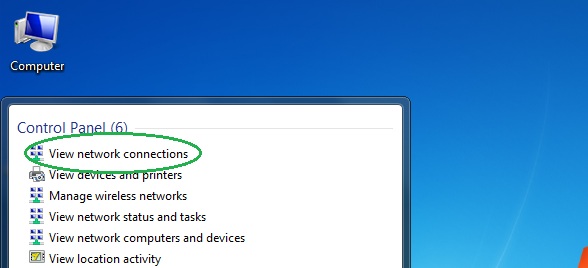
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
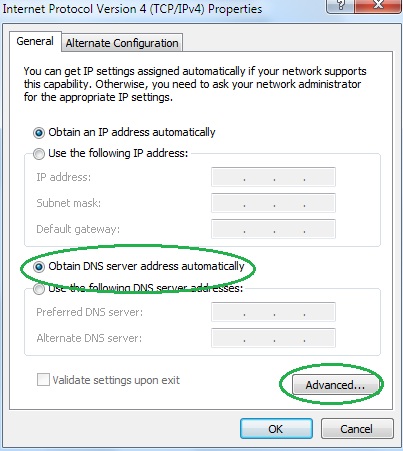
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
