Welcome, to our Securesurf.biz Toolbar removal guide. The following instructions will aid you in removing the unwanted software and the toolbar it creates from your PC.
We have created the article below with the idea to help you understand the characteristics and effects of Securesurf.biz. This program is classified as a typical browser hijacker. In fact, this means that it can be able to really change the way your browsers (Firefox, Explorer, and Chrome, for example) behave and look. This software might alter their default search engine and usual homepage; sudden redirections to various web addresses might begin and Securesurf.biz could launch the production of a great number of online ads – pop-ups, boxes, banners and so on. All the information you need to know has been shared with in the article and the guide you will find below.
Browser hijackers as a whole
In the previous paragraph we described what a typical infection with a hijacker leads to. Note that only your browsers are the ones that are affected, everything else will be safe in case of such contamination, so you have no real reasons to be worried. Nevertheless, such programs might extremely annoy you with the constant stream of pop-ups and the constant circle of redirections. Another possible feature programs like Securesurf.biz may show is their ability to predict what kind of ads you might want to see based on your surfing history, and will then broadcast only them or mainly them. Such activities are often perceived as intrusive by many of the affected users. As a result, this software has been regarded as potentially unwanted and may have a mostly negative reputation. In spite of this browser history-reviewing tendency, Securesurf.biz and its siblings normally do not have any malicious or disturbing features. For instance, in case of a Ransomware-provoked infection, your files could be in serious danger, facing the possibility of being locked up and you – possibly having to deal with ransom demands. In case of an infection with a hijacker, nothing like encryption, harassment or actions typical for viruses could occur.
Is Securesurf.biz legal if it is mostly harmless?
Indeed, this program is legitimate because it is a part of marketing strategies. This is just a way of advertising services, websites and products. It is based on legal agreements between web developers and service providers/ product producers. The way this scheme works is the following: the more ads you see, the more efficient the promoting process is expected to be and the programmers of hijackers could get paid more.
If this is not a virus, could this program sneak into your system unnoticed?
Actually, browser hijackers NEVER get incorporated into any system without at least indirect approval from the user. This could mostly happen in case the hijackers are included in program bundles. A bundle is any free mixture of apps, games and programs that you can download directly from the Internet. In this case the potential victim user is particularly interested in some of the components of the bundle – either an interesting program, or a new game, and wants to try them as soon as possible. This makes most users quite impatient and they can make the mistake of installing any program bundle in the quickest or the easiest, but totally improper way. The only safe method of installing whatever software you download for free or buy is to go with the Advanced installation feature instead of the Default one. Only having the chance to manually choose the to-be-installed components of a bundle or features of a program could save you from possible annoying or even dangerous infections. That is why you are supposed to avoid all shortcut sorts of installation and all of the wizard options that provide them – the Automatic, Easy, Quick or Default ones.
Some more valuable advice
For your own safety, please, try to develop healthy cyber habits as soon as possible. They include purchasing and installing, as well as regularly updating the best possible anti-virus program you can find. Such a great-quality product will include Internet security features that will probably block Adware and hijacker sources. Also, another quite simple but really useful tip is to just avoid all suspicious web pages, torrents and shareware as often as possible as they could also contain ad-producing software. Maybe you will consider turning on your firewall and your pop-up blocker to at least limit the webpage-hosted advertisements. For the safe and successful removal of Securesurf.biz please check the Removal Guide below and implement all the instructions there.
Securesurf.biz Toolbar Removal
I – Uninstallation
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot Securesurf.biz, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
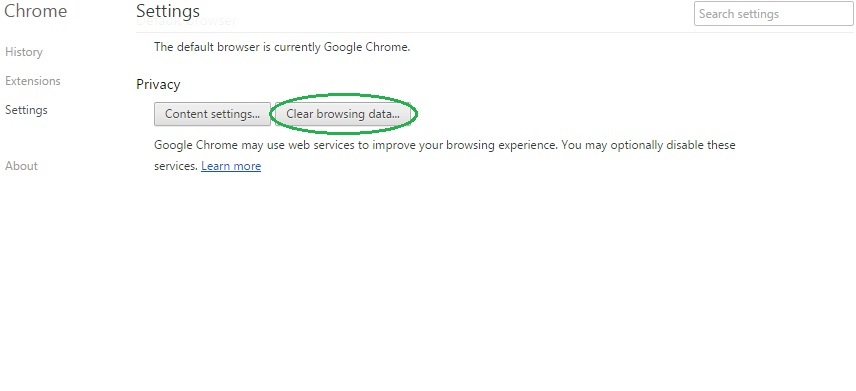
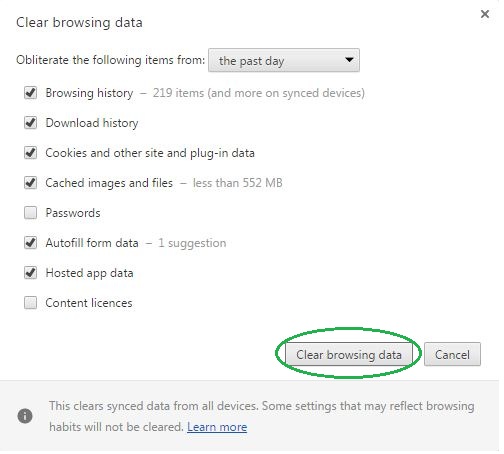
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
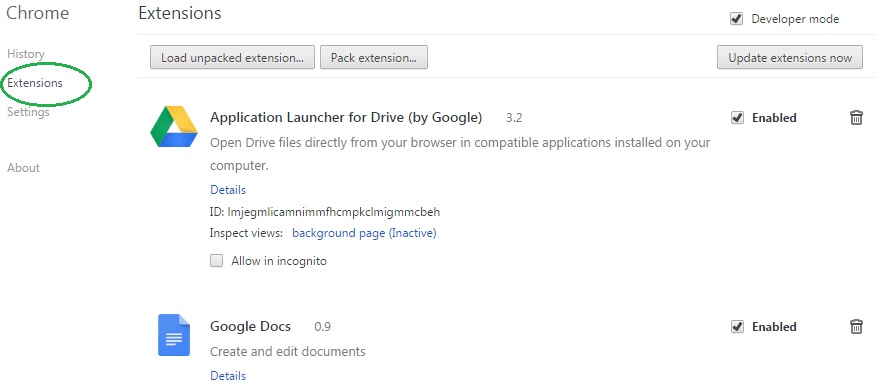
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Securesurf.biz on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Securesurf.biz might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Securesurf.biz, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
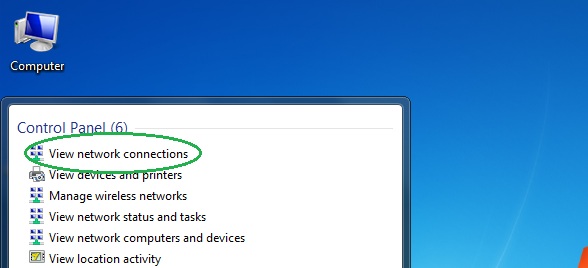
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
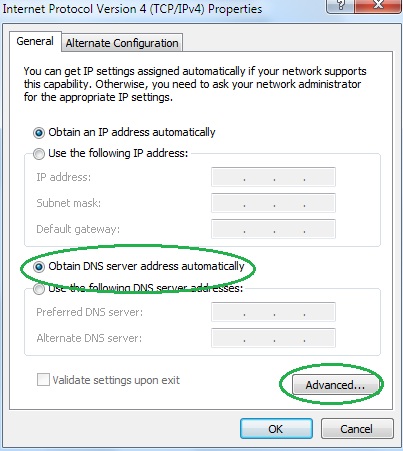
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
