[bannerTop]
Can’t Remove Qis.Balloonchatted.com hijacker virus? This page includes detailed Qis.Balloonchatted.com Removal instructions
Briefly speaking, this software may be a legal version of the annoying browser hijackers which in spite of being considered harmless, can terribly irritate you as their effects are primarily centered on generally changing your browser apps:
– by causing a lot of redirection to various online locations once you attempt to open a given website and as a result, rendering your browsing a rather unpleasant experience;
– by causing a giant variety of pop-ups and different other ads to appear on your screen as you are surfing the Internet;
– by displaying entirely new homepages and search engines (the ones this hijacker has been set to promote).
Moreover, each single browser might become a victim of this software version. It is true that neither Chrome; nor Explorer, Firefox or Opera will be able to avoid such an infection. Browser hijackers represent the most common advertising type of software together with other programs referred to as Adware. Both kinds of advertising software are generally considered unwanted although they actually do not damage the infected devices in any manner. They are merely able to modify all of your browsers in the aforementioned ways and that’s all.
What does ‘advertising software’ actually mean?
In general, this title suggests that Qis.Balloonchatted.com and its siblings in fact have solely promotional functions. Actually, they’re created simply to advertise services, products, homepages, search engines, web pages and other kinds of different product. All the interested manufacturers and distributors of the above have worked in cooperation with programmers to create legitimate software packages for online advertising. Therefore, Adware and browser hijackers have been first created. As far as these ad-generating programs are concerned, all the parties involved benefit from them. The manufacturers get their products popularized, and software developers earn some considerable extra amounts of cash, depending on the efficiency of their hijackers. The advertising efficiency is generally measured by the number of redirections and advertisements that the programs like Qis.Balloonchatted.com invoke. Really, this is the basic reason for the usually irritating nature of such software. These programs simply need to display as many pop-ups as possible on your screen and send you to more and more websites that need popularizing.
Is Qis.Balloonchatted.com like a virus?
As we’ve explained from the start, browser hijackers are legal programs. No real virus is legal. As an example, Ransomware and Trojans are considered very dangerous and may end in lots of disastrous effects. Really, this is not the common case with Qis.Balloonchatted.com – this program can’t really result in any malicious consequences. This is how you may find yourself catching an infection with a hijacker:
Most times the exact strategies programmers use to spread hijackers can be perceived as not particularly trustworthy and even intrusive. Although this type of advertising software is generally harmless, no user needs to have their surfing experience compromised by any ads and redirecting, and will not be willing to voluntarily install such a program on their devices. However, Qis.Balloonchatted.com is legitimate and as such, it needs to get your direct or indirect permission to become an element of your system.
The usage and appearance of program bundles for spreading hijackers and Adware:
Program bundles have emerged with the purpose of distributing browser hijackers and Adware lawfully by tricking you to put their entire content into your PC – together with the ad-producing package within them. These bundles are free combos of programs and apps you’ll usually be able to download from the web for free. Usually, they comprise of varied and attention-grabbing games and programs that you may be interested in having. There’s commonly a trap, though. In case you select to put in such a free set by utilizing the Automatic, the Default or the Recommended installation feature, you will let the full content of the bundle in, and most likely your device will get infected by Qis.Balloonchatted.com or a similar program. Nevertheless, if you remain calm and perform the installation via a secure method, you’ll be immune to ad-broadcasting programs. To complete an installation process in the correct way, there are only 2 possible options you can choose when the installer appears. One is the Advanced, and the other is the Custom. Provided that you choose any of them, you’ll be asked to undoubtedly select the particular apps, games and program that you indeed need to get installed on your device.
Removing and avoiding programs like Qis.Balloonchatted.com:
In order to get rid of Qis.Balloonchatted.com, follow the information in our Guide below. For the aim of staying far from such programs in the future, always keep in mind the importance of mastering the aforementioned way of safely installing any piece of software, as well as avoiding the other possible sources of ad-related programs such as torrents, file-sharing web pages and other contaminated ads on the Internet.
Qis.Balloonchatted.com virus Removal
I – Safe mode and revealing hidden files
II – Uninstallation
[bannerMiddle]
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
If you are unable to spot Qis.Balloonchatted.com virus, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
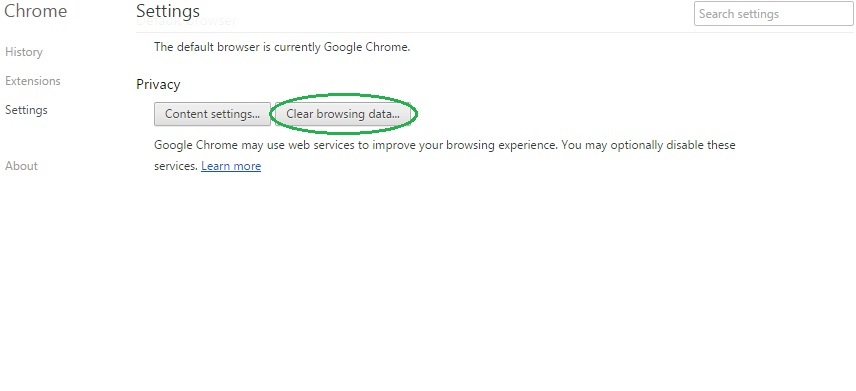
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
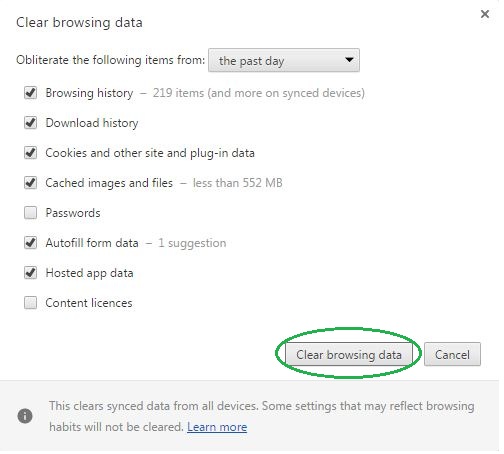
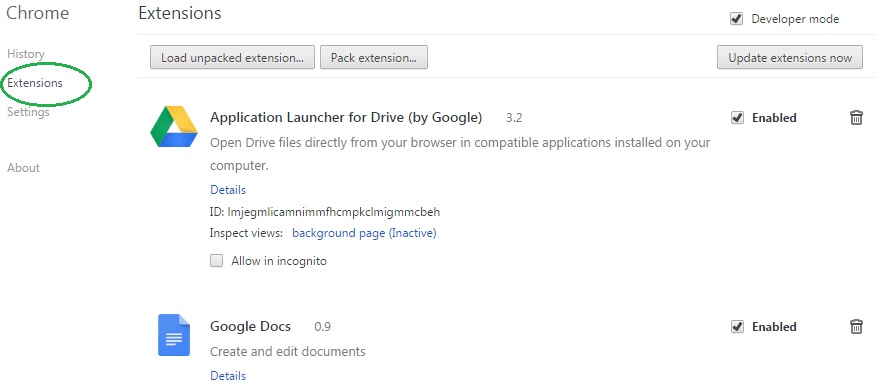
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Qis.Balloonchatted.com virus on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Qis.Balloonchatted.com virus might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Qis.Balloonchatted.com virus, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
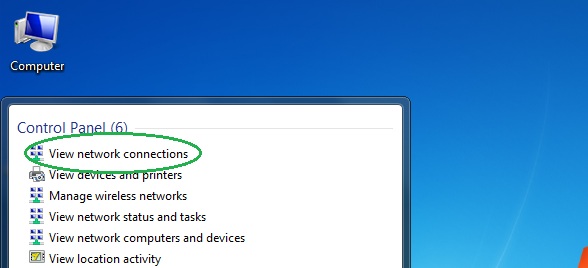
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
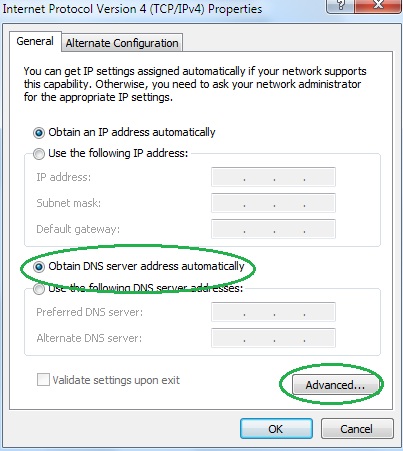
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
