[bannerTop]
Welcome to our Newtab.win “Virus” removal guide. The following instructions will aid you in removing the unwanted software from your PC.
In the text that follows we will be describing a very irritating program called Newtab.win in details. A piece of software like this one might lead to some annoying changes your browser’s appearance and manner of functioning. Some of the consequences of its actions may include a kind of abrupt redirecting to diverse web locations; the constant broadcast of various online ads, no matter whether you use your Chrome, Firefox, Opera or Explorer browser to surf the web. In addition, they may also result in the unauthorized substitution of your usual homepage and search engine with new, totally unfamiliar ones. Speaking of browser hijackers, it is essential to point out that these programs may only infect your browser apps and have nothing to do with any kind of viruses. Their actions are merely marketing driven and all the changes that they inflict may be explained by the fact that their developers have been paid to popularize, for instance, a website, a search engine, any product, homepage or service. Such advertising software is legitimate, though. You can read more about this kind of software below.
What makes programs like Newtab.win different from malware:
The usual virus versions like the ones based on Trojans or Ransomware can perform something harmful once they have been installed on your computer. Some of them may encrypt files, others could destroy them or format all your disks and drives. Some of the known viruses harass you into paying a ransom, others can drain your bank accounts in some way. Some malicious programs could target data, and others may hijack your identity and use it for all sorts of dishonest purposes. You shouldn’t expect anything like that from a hijacker such as Newtab.win. What it may sometimes do is check your most recent browsing search requests, and adjust the production of ads to your supposed interests. This may at first appear intrusive, but still, such a research might be useful to you. In this way you are going to get the best offer for what you have been searching for. However, some users think that such an intensive research is shady, thus they are afraid that some of the pop-ups may actually lead to contagious web pages. That is why hijackers have the reputation of potentially unwanted software.
Possible ways of catching Newtab.win:
A hijacker may be hiding almost everywhere on the web. They could be inside torrents or incorporated into diverse web platforms. They may get distributed with the help of spam or fake ads. The most common source, however, is every free program bundle on the Internet. As you might be expecting, a bundle is a set of different programs bundled and spread together. Inside it there could be various games, apps, Adware programs, browser hijackers and a lot of other types of software. Nonetheless, remember that simply downloading any bundle is never the real cause for an infection. The most common cause for infection is improperly installing it.
How to install a program bundle so that to avoid the potential hijacker inside it:
Just make sure that you carefully follow the tips below and you will not be affected by Newtab.win or any other similar program. When the installation wizard appears in front of you, you will see the installation features available. From all the displayed ones, search for the Advanced (sometimes Custom or Customized) option. In order to complete the process properly, use only this feature. That is the only way to get to choose what from the bundle to install and what to leave out. Make sure that you try to avoid all other installation options. They might have different names, such as Default, Automatic or Quick. None of them are really good for your system, as by using any of these ones you will have no choice of what to leave behind and what to install on your PC.
Advice on prevention and removal
Beside the right way of installing any kind of software that you want to try or use, try to stick to these steps to minimize the risks of getting an ad-producing program:
- Try not to use any of the other potential sources of hijackers;
- Ensure that your OS functions well and is up-to-date;
- Check whether you have a good anti-malware program installed on your device. If not, buy and install a good-quality program immediately.
In case an infection has already occurred, we advise you to follow the steps inside our Removal Guide below.
How to Remove Newtab.win “Virus”
I – Safe mode and revealing hidden files
II – Uninstallation
[bannerMiddle]
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
If you are unable to spot Newtab.win, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
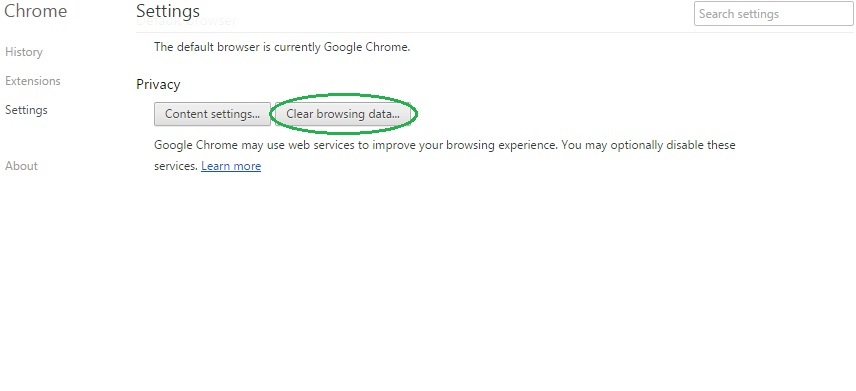
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
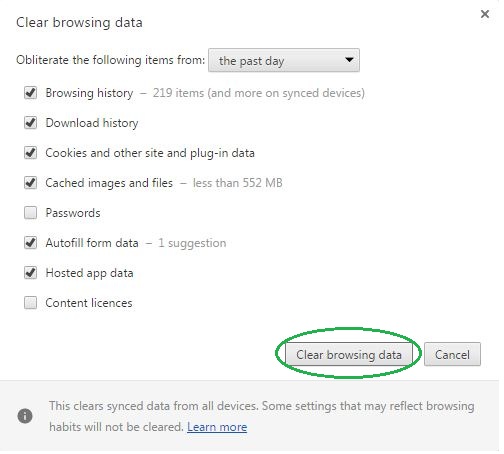
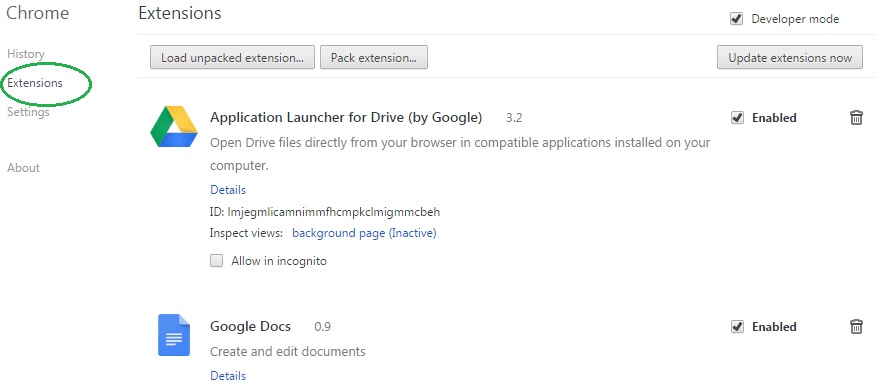
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Newtab.win on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Newtab.win might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Newtab.win, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
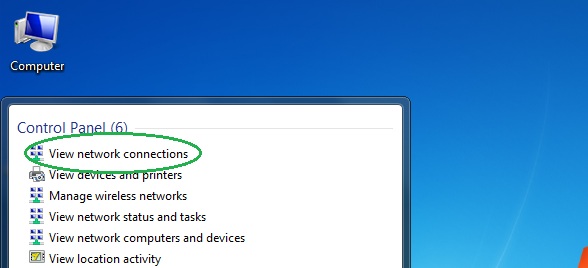
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
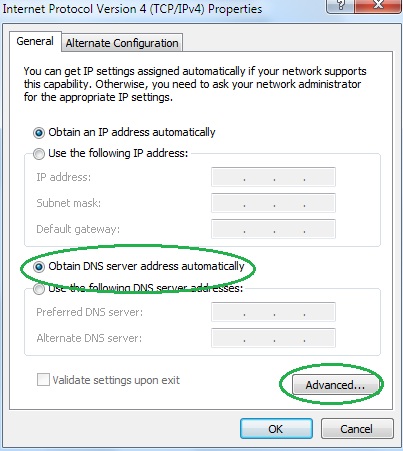
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.

