[bannerTop]
Welcome to our Launchpage.org “Virus” removal guide. The following instructions will aid you in removing the unwanted software from your PC.
Below we will be discuss browser hijackers in general, as well as one of their newest representatives in particular – Launchpage.org “Virus”. Such a program is known to broadcast pop-ups as often as you try to surf the web. In addition, it can also send you to websites you had never had the intention to visit; and set put new and often unfamiliar homepages and/or default search engines on all of the browser apps you have installed – Firefox; Opera; Chrome and/or Explorer. We have gathered the information in the following article to help you realize the nature of the ongoing infection and how to deal with it safely and successfully.
What if the term “browser hijacker” doesn’t ring a bell?
In sort, this kind of software may have some rather irritating features, such as the generation of pop-ups; the redirection it might cause, and some even more annoying features such as:
- conducting a sort of research into your browser apps records, and defining what kind of content you seem to be interested in the most;
- broadcasting such a great number of ads that your device might start freezing and crashing, because of the intensive consumption of RAM and CPU.
Will a program like Launchpage.org actually “hijack” any files from your PC? Are these programs dangerous viruses?
No browser hijacker resembles any known virus type. Malware and advertising software are not related in any way. In fact, there are some really serious differences between Launchpage.org and any normal virus, such as a representative of the Ransomware or the Trojan malware categories. To be completely precise, Trojans cause some data destruction or information theft from your PC. The other most dangerous virus programs – the ones based on Ransomware, are notorious for encrypting files, and then asking for a ransom. These malware categories might invade your system on their own. Thus, no permission is needed from your side, even an unwillingly/ unknowingly given one.
If Launchpage.org is not malicious, what’s its real purpose?
Browser hijackers have mainly promoting functions. All the redirections, the newly set homepages and/or search engines, as well as the big number of generated ads seem to advertise all types of products. Programmers are paid to create hijackers and advertise services, software and all sorts of products in the most efficient way. Also, the developers get their payments in accordance with the exact number of the pop-ups, which they generate, as per the popular remuneration system better known as the Pay Per Click scheme. All the annoying activities any hijacker could conduct are completely legal and do not break any laws and regulations.
What about the way of spreading browser hijackers? How are you likely to catch a program like Launchpage.org?
The distribution methods, used by the developers of these promoting programs may also appear quite shady. Browser hijackers are not malicious; however, the modifications they may provoke can annoy the affected users to a great extent. The possible browser hijacker sources may include:
- Shareware websites; video-sharing and torrent-sharing web pages: Nearly all illegal web pages represent potential hijacker sources. The people behind them are able to distribute movies, software and other products for free, mainly because they earn money out of the advertising software they often spread.
- Contagious pop-ups: Often just a click on a random ad while you are surfing the Internet may result in your redirection to contaminated online locations, where you may catch browser hijackers.
- The most typical possible sources of Adware and browser hijackers are the so called software bundles. In fact, they represent combos of free apps, games and programs, which you can access on the web. What you need to know about them is that simply downloading a bundle will not result in an immediate infection. Installing it improperly is likely to do so, though.
The way to install a bundle or a program properly, so that you can safely avoid advertising programs?
Always bear in mind that the installation wizard features you use actually do matter. Ensure that you always go with one of the most elaborate features like the Custom/ized /, or the Advanced ones; which typically provide you with the chance to select the particular features and components of the bundle that you want installed on your PC. It is essential that you should not go with the Default; or the Quick installation options, as they will deprive you of the opportunity to choose what to put inside your system.
How to remove a hijacker?
In case you decide to do so, use our Removal Guide below.
Launchpage.org “Virus” Removal
I – Uninstallation
[bannerMiddle]
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot Launchpage.org, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
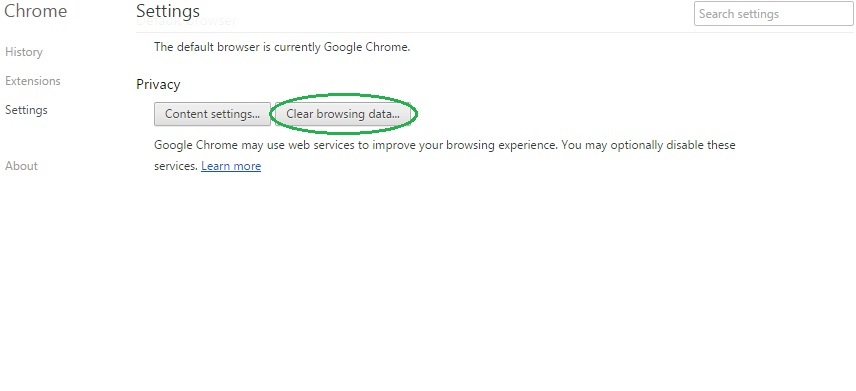
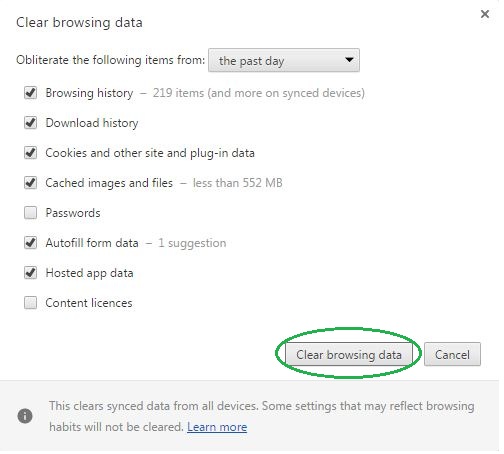
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
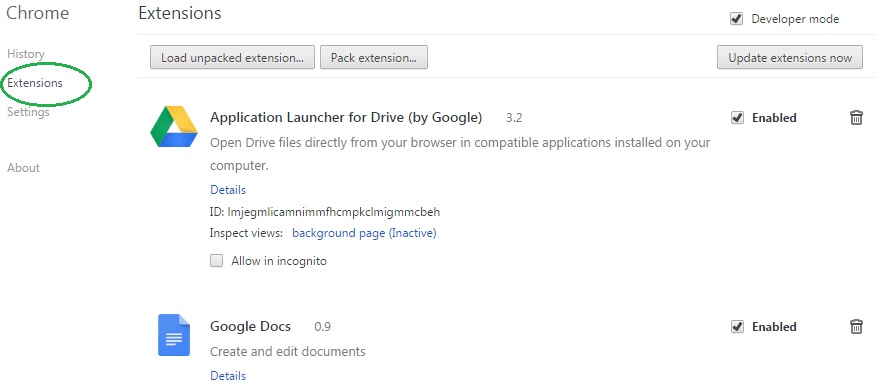
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Launchpage.org on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Launchpage.org might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Launchpage.org, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
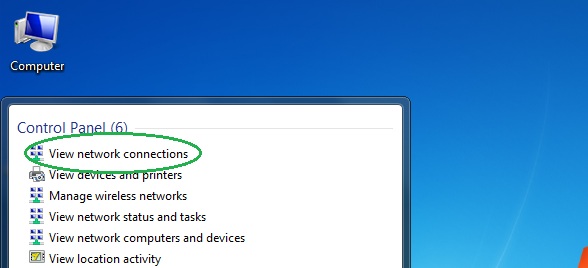
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
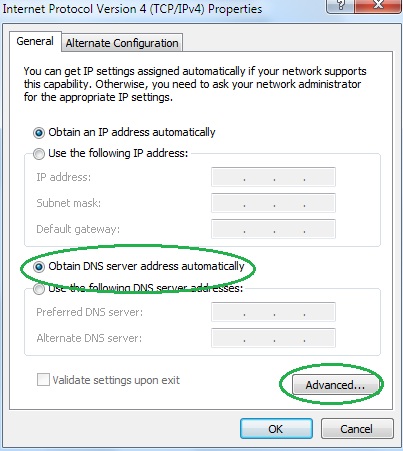
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
