[bannerTop]
Welcome to our Kipuu.cn “Virus” removal guide. The following instructions will aid you in removing the unwanted software from your PC.
One very common problems that users often have with their Chrome, Firefox or IE browser is when it is invaded by a program that changes its homepage, search engine and ads new toolbars without the user’s agreement. A recently released program called Kipuu.cn that has been reported to do that and it will be the focus of our this article. We will help our readers who have had this piece of software installed onto their PC get a better understanding of what it is and what problems it might cause. Additionally, we have prepared a detailed guide manual in which we explain how the unwanted program can be uninstalled and removed from the computer so that you can do that yourself without the need to take your PC to an IT specialist.
The Browser Hijacker type of programs
Kipuu.cn is a program that is usually categorized as a Browser Hijacker. Those are programs that are mostly used as online advertising tools. Some of them might appear to posses certain useful features but in most cases they are nothing but a pain in the neck during the time they are installed onto your PC. This is because the main purpose of most Browser Hijackers is to profit their developers through different aggressive advertising techniques. While this is usually not harmful to your PC, it can be really frustrating to have your browser taken out of your control and heavily modified by the unwanted software. Therefore, the best possible course of action when encountered with a Browser Hijacker is to have the intrusive program removed as soon as possible.
How harmful?
Even though Browser Hijackers can be really annoying and invasive, an important note that must be made with regards to them is that they are not actual PC viruses. Many think that Kipuu.cn is some sort of malware but the truth is that most Browser Hijackers are quite harmless. Real viruses like Ransomware and Trojan horses are what you should really be concerned about. If it’s just Kipuu.cn that you’re currently having problems with, then there should be no reason to worry. As a matter of fact, despite their intrusive nature, most Browser Hijackers are generally legal. The same surely cannot be said about actual malware like the examples we mentioned above (Ransomware, Trojan horses, and so on).
Potential issues
Regardless of their relative harmlessness, Browser Hijackers are still some of the most annoying and nagging programs that you can run into. We already mentioned some of the intrusive traits that most of them posses. However, having your browser homepage and search engine changed are certainly not the only problems that you might have with a program of that type.
- Generally, Browser Hijackers have a function that allows them to monitor your online searches. Later, they use the info to display you ads that are relevant to your personal interests and preferences. The more ads you click on, the higher the revenue generated by the Hijacker for its developer.
- Probably, one of the most problematic aspects of having Kipuu.cn installed onto your PC is the fact that your browser is very likely to be invaded by numerous obstructive pop-ups, banners and sometimes even fake error messages that tell you to install some obscure PC optimization program in order to deal with the errors (that are probably non-existent). Our advice for your is to avoid any interaction with those ads because you never know where they are going to redirect you to.
- Another very annoying problem with some Hijackers is that they can really slow down your PC. Oftentimes, the system resources consumed by the Hijacker’s processes can cause system freezes and crashes. The only way to stop this is to disable the unwanted program by uninstalling it and removing all traces of it from your PC.
Tips for future use
Now, that you have learned what Browser Hijackers are, you must be taught how to prevent them from getting installed in your system. The bad news is that those programs are so widely spread that you can never know when one is about to get onto your machine. The good news is that if you follow several simple but crucial guidelines, your PC’s safety and security would be significantly boosted and the chances of landing a Hijacker – greatly decreased.
- Ensure that your browsers always ask for a permission when a file is about to get download. You should never allow files to be downloaded automatically or you you won’t be able to prevent a Hijacker from getting inside your PC.
- Do not visit (or download stuff from) websites that you are not sure whether you can trust and do not interact with e-mail letters or other forms of online messages if you think might be spam.
- Only install new software once you’ve checked the setup wizard for program bundles. If you find that there have been added programs to the main install, take a close look at them and if you think that they look like Hijacker or some other form of PUP (potentially unwanted program), make sure to uncheck them before continuing. In many cases, you might need to access the Advanced installation menu to see if there’s anything added to the main program so make sure to opt for that if such a menu is available.
SUMMARY:
| Name | Kipuu.cn |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Annoying online ads, new browser search engine and changed homepage. |
| Distribution Method | Mostly through spam messages/emails, torrent websites and file-bundling. |
Kipuu.cn Removal
[bannerMiddle]
I – Uninstallation
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot Kipuu.cn, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
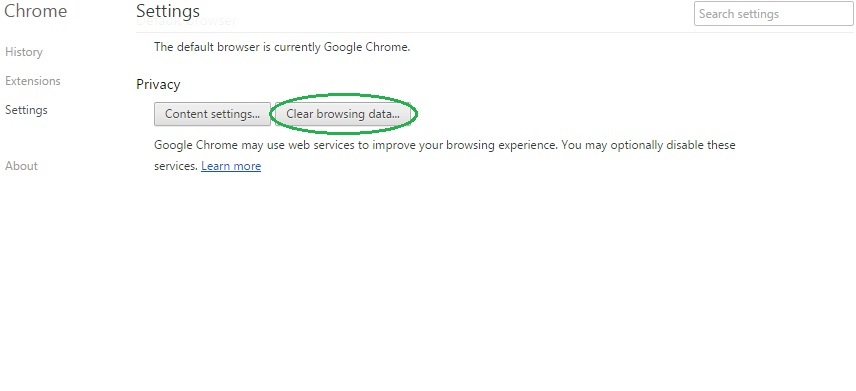
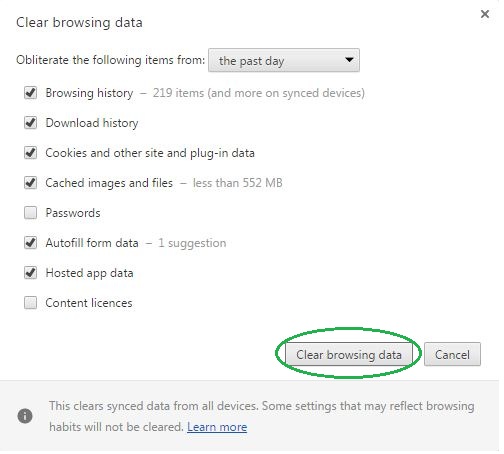
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
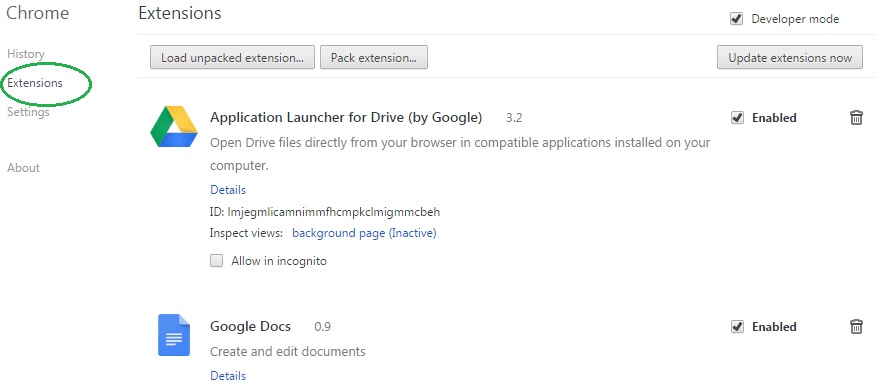
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Kipuu.cn on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Kipuu.cn might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Kipuu.cn, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
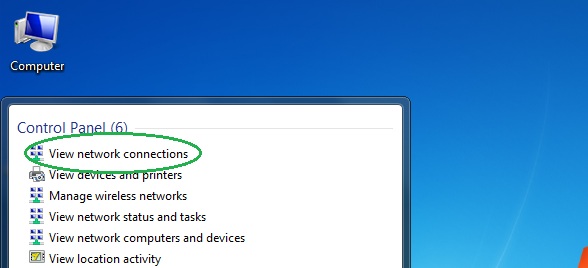
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
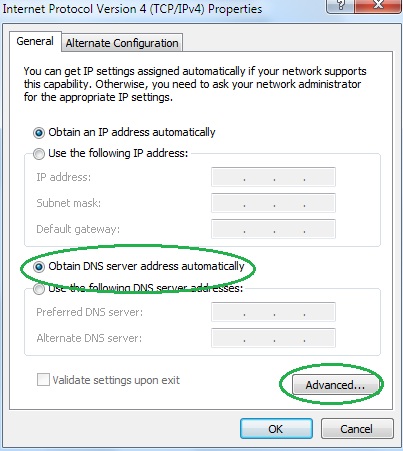
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
