[bannerTop]
Welcome to our Jamper Chrome Virus removal guide. The following instructions will aid you in removing the unwanted software from your PC.
Perhaps lately you have been constantly annoyed by one specific program – Jamper Chrome Virus. The following paragraphs have been created with the main purpose to give some adequate answers to all your questions about this program. For instance, what browser hijackers are and why Jamper Chrome Virus is classified as one. Moreover, we are going to talk about the reason why such software will normally infiltrate only your browser apps (like even the most common ones – Firefox, Explorer, Chrome); as well as about all the functions which usually characterisze it. Such ones are its capability of generating many irritating ads; sending you to a place on the web you hadn’t intended to load; or setting some totally different and unknown homepages and search engines to your browser apps. Furthermore, we have also elaborated on a number of prevention tips to assist you in staying away from this software kind after you have succeeded in dealing with the current infection. A specialized removal guide to help you remove the infection is also included. Check out the whole article!
Essential info about Jamper Chrome Virus:
Generally speaking, Jamper Chrome Virus falls into the browser hijacker software category, meaning that this product might be capable of performing some irritating modifications regarding your browser apps. As it may be concluded from its name, such software could alter most of your browsers’ settings. The inflicted changes may lead to the the broadcast of lots of ads; as well as to some intense annoying redirecting, and/or to the setting of some unknown search engines/homepages. These are the possible effects Jamper Chrome Virus may have on your system.
Potential suspicious effects:
Although the general functions of hijackers have already been discussed above, there may be some activities that Jamper Chrome Virus could do, which may really be suspicious – like the thorough research on your browsing preferences. As a result of reviewing your browser history records, the ad flow which may be overwhelming your browser could be adjusted to show you only the ads of the products (services) you are likely to be interested in. That’s why some experts see this kind of software as potentially unwanted.
Is there any relation between hijackers and the real forms of malware (such as Ransomware)?
Precisely speaking, browser hijackers are NOT related to any malicious program, which comes from the fact that they do not have any actual harmful features. The specifics of the famous malware categories such as Ransomware and Trojans may include researching your data storages and encrypting those of your files, which you most regularly access. Furthermore, the normal viruses, for example the ones from the Ransomware group, are more than capable of completely crashing your whole system; or deleting some of your essential data there; as well as – of formatting all of your drives. One more typical characteristic of the popular types of malware, instance – the Trojans, is their ability to spy on you and track all your activities online and out of the web immediately after the virus has infiltrated your device. Nothing like that has ever happened as a result of an infection caused by a hijacker.
How does the process of infecting your PC conducted by a browser hijacker occur?
The probable ways of distributing Jamper Chrome Virus are normally directly connected to the reasons why such software is created in the first place. Programmers are very likely to spread browser hijackers and other ad-broadcasting software by collecting them inside bundles along with many other programs, games, and apps. In general, such software combinations can be reached, downloaded and used free of charge. The reason for that is the fact that their developers get paid based on the number of the ads their hijackers generate later on. Nevertheless, the current infection can NEVER occur just because you have downloaded a given software bundle. Such an infection could occur only on the condition that you install a given bundle using a rather time-saving and safety-disregarding installation method, which deprives you of choosing what you really need on your PC and what you can leave behind.
If you really need your PC to remain hijacker-free, it is vital that you should choose a more thorough installation feature – the ones you can choose and trust are called either the Custom, the Customized or the Advanced. That’s how you will be granted full control over the installation process of any bundle or a separate program, and you will be able to manually select which features and programs you are going to put inside your system.
If a contamination process has already occurred, and you need to remove Jamper Chrome Virus from your system, simply follow the instructions in the guide right at the bottom of this article.
SUMMARY:
| Name | Jamper |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | You PC could become slower and your browsers – modified. You may see too many ads or get redirected too often to pages you don’t want to visit. |
| Distribution Method | Inside torrents; shareware, ads, bundles. |
Jamper Chrome Virus Removal
I – Safe mode and revealing hidden files
II – Uninstallation
[bannerMiddle]
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
If you are unable to spot Jamper Chrome Virus, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
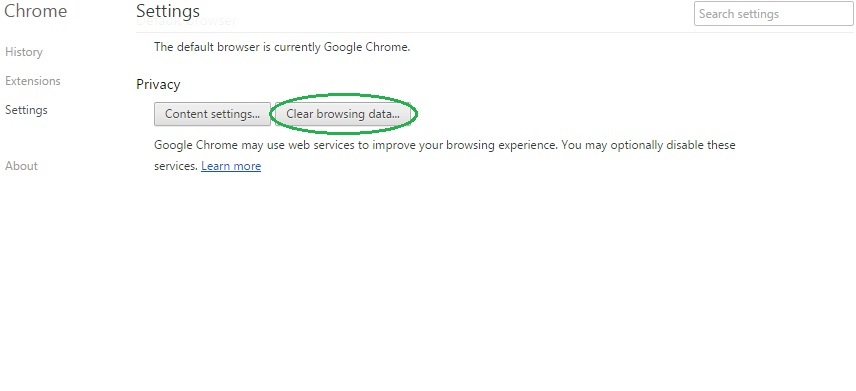
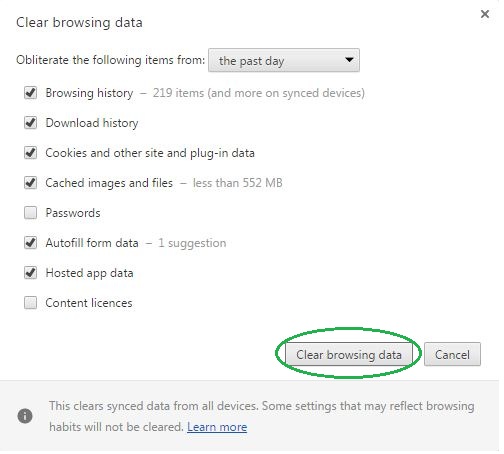
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
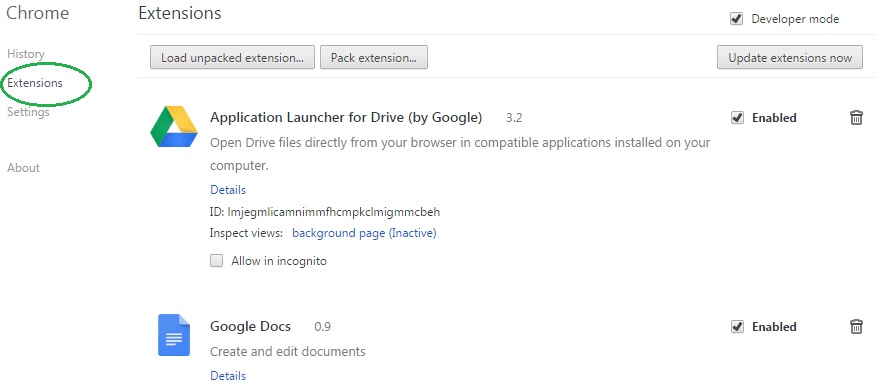
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Jamper Chrome Virus on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Jamper Chrome Virus might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Jamper Chrome Virus, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
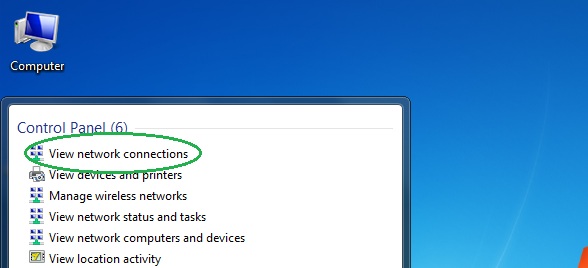
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
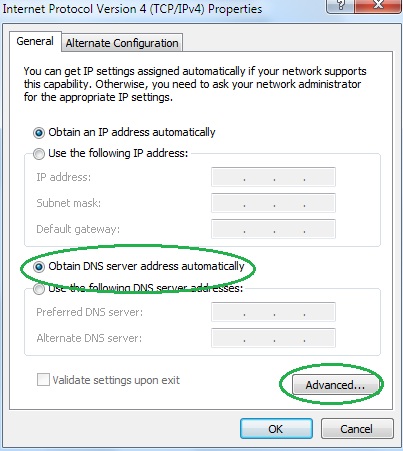
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
