[bannerTop]
Welcome to our Mans-find.org “Virus” removal guide. The following instructions will aid you in removing the unwanted software from your PC.
Mans-find.org “Virus” represents a typical browser hijacker. In case you are wondering what such a program could do to your computer, certainly, it may “hijack” all the browsers that you have installed on your system. Neither Chrome, nor Explorer or Firefox can escape its effects, which includes setting entirely new homepages and search engines; some redirecting to other, often unfamiliar pages; and the generation of awfully many online ads in the form of pop-ups, boxes, colorful banners, etc. In fact, we have assembled the following article with the simple purpose to help you realize what kind of a program you will be dealing with and how to do that quickly and successfully.

Browser hijackers – what we should know about them. How do they act? Are They malicious?
First of all, you have to understand that browser hijackers may only target your browsers. In fact, it doesn’t really matter whether you use Firefox, or Opera, or Chrome, once such a program has become incorporated into your system, all of them will be affected. The changes such software usually provokes have been described above and consist of no real harmful effects. Fortunately, this hijacker is not a virus. It could only do what we have described above – slightly modify your browsers. To illustrate this statement with an actual example, we are going to show you the great difference between Mans-find.org and a Trojan horse virus, as well as a Ransomware-based malicious program. You already know what hijackers do best. Their typical effects are in no way connected to what a Trojan or Ransomware could achieve:
- Trojans are malicious and have various deeply concerning purposes – they could steal important credentials, personal information, or drain your bank accounts. No hijacker has ever done that.
- The viruses based on Ransomware do not affect your browsers; they do affect your data. No data is safe when it comes to an infection with Ransomware. Such programs are used for making all the files you regularly use completely inaccessible to you. Then the program usually demands ransom to be paid for the hijacked data. See, this is what we call real harassment.
Hopefully, we have proven that hijackers are really harmless compared to real malware like Trojans and Ransomware.
Still, could hijackers sometimes exhibit rather confusing or disturbing features?
Unfortunately, browser hijackers have been identified as potentially unwanted programs because they may sometimes perform some inexplicable activities on your PC, which many users may consider a little intrusive. For instance, when Mans-find.org accesses your browsers, it could instantly reach the search request databases of these apps. As a result, the constant flow of pop-ups that you are experiencing may only consist of ads connected to your recent / previous search requests. Such prying into your tastes and browser history is usually considered rather disturbing. Another sometimes annoying feature of most of the existing browser hijackers is that they may slightly overwhelm you with the online ads they may generate. At some point they could produce so many pop-ups and banners that your computer could seriously slow down. Also, the redirecting processes they invoke may be so many that your browser could totally stop working. Such effects are quite rare, though.
Why do programmers create programs like Mans-find.org? How do they distribute them?
In fact, these programs are completely legal – they do not break any laws, they just advertise things. Consequently, developers agree to create them in order to ensure some additional profit for themselves and their business. The more ads and redirections are provoked, the more money the program’s creator earns. Hijackers are most often distributed inside program bundles – free sets of software that you may download anywhere on the web. However, these mixtures of apps and games are not harmful, they may just contain irritating programs like Mans-find.org. In order to avoid the potential annoying software inside them, learn to install bundles right. The only way to do that is by choosing the ADVANCED (sometimes CUSTOM) installation features of a given wizard. This will save you from such disturbing programs in the future.
How could we handle a browser hijacker?
Actually, we can easily remove such unwanted software by carefully following the steps inside a reliable Removal Guide. Ours is available for you below – just after you read the characteristics of Mans-find.org in the table. The instructions there should assist you in getting rid of this hijacker. In case something doesn’t work in your case, please do not hesitate to share that with us by leaving a comment. Our experts will gladly make the instructions work in your specific case.
Mans-find.org “Virus” Removal
I – Uninstallation
[bannerMiddle]
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot Mans-find.org, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
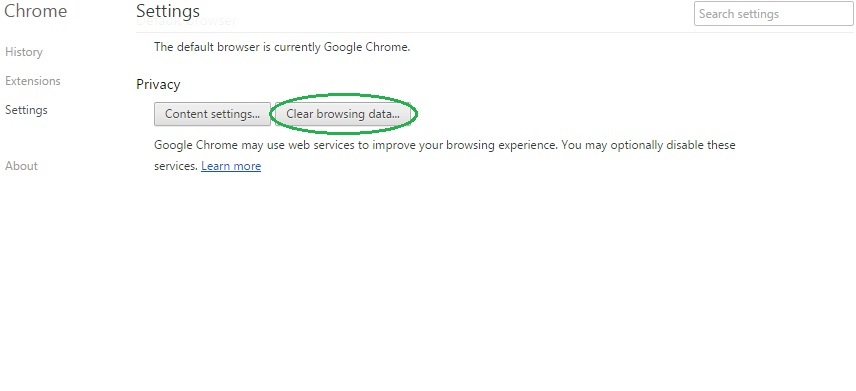
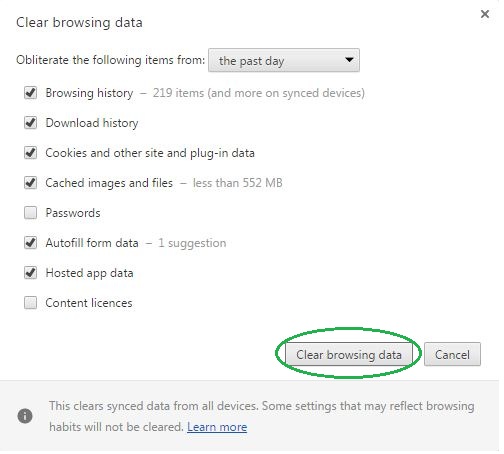
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
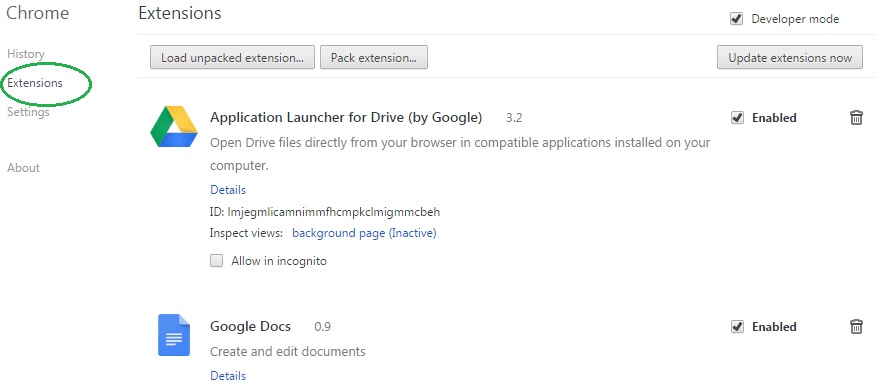
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Mans-find.org on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Mans-find.org might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Mans-find.org, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
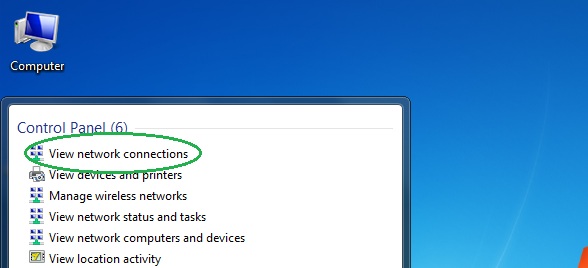
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
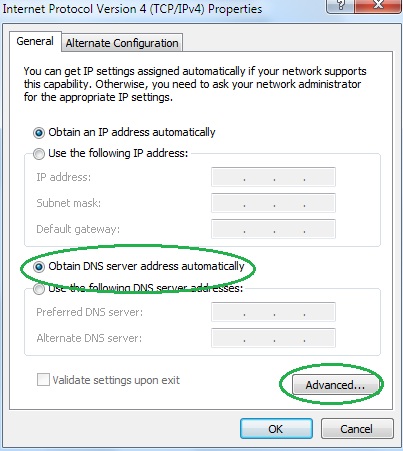
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
