[bannerTop]
Welcome to our Linenews.org “Virus” removal guide. The following instructions will aid you in removing the unwanted software from your PC.
Dealing with browser hijacker isn’t exactly anyone’s ideal pastime. But, unfortunately, now and then we may end up with the annoying piece of software on our PC and most of the time – it’s our own fault. In this article we’ll be looking at a specific member of the browser hijacker software family – Linenews.org. Just like other representatives of this category, Linenews.org may also introduce certain unwanted changes to your favorite browser, be it Firefox, Chrome, Edge, Explorer or something else. It’s likely to change your browser homepage and set a new search engine as the default one, which in addition may also redirect you to various promotional pages. What’s more, no matter what you try to do, these changes will be set in stone as long as the said program remains on your PC. If this sounds exactly like what you’ve been experiencing lately and you would like to learn how to effectively remove Linenews.org and all of its undesired effects on your machine, then read on and proceed to the instructions in our removal guide below.
Browser hijackers: What they’re really after
Software of this type acts in a way that is dictated by its developers’ desire to profit. What we mean by that is that these programs are in essence a very effective business model. By promoting certain products and services with the help of the endless popups, banners, hyperlinks, box messages and other online ads, they earn revenue for their developers. Usually, to make this work, the system used is the Pay Per Click scheme, which ensures that for every one of your clicks on the said ads, the developers make a certain amount of money. With that in mind, it’s easy to see why the many popups and banners are, in fact, so many and oftentimes – so aggressive. Surely you must have at least once clicked on an ad by sheer mistake, after it just appeared out of nowhere.
But in addition to this blunt approach, the developers often resort to a little less obvious one. They often program their hijackers with the ability to look through your browsing history and record information regarding your recent online search requests, pages you’ve visited and the type of content you tend to like and share on social media, etc. Thanks to this data, Linenews.org and other like it can determine where your latest interests lie. This will in turn tell them how to modify the flow of ads so that it suits your personal preferences. And all of this is done with the aim to attract your attention to at least some of the ads, making you click on them. It’s apparent that this approach isn’t exactly favored by the online community, mainly because it’s unauthorized by users and is thus considered a privacy invasion.
Do hijackers pose a threat?
The short answer is no; not directly, anyway. Many users mistakenly jump to the conclusion that Linenews.org and other programs of the same category are viruses or otherwise malicious and capable of inflicting harm. There’s not enough proof to make such drastic claims, but due to their questionable means of distribution, the above tactics of collecting info on users and the potential of exposing you to other threats, security experts tend to refer to browser hijackers as potentially unwanted programs. This puts them somewhere in between genuine viruses like Trojans and ransomware and harmless programs. With that being said, we do recommend that you be careful as long as this program remains on your PC. Try to abstain from interacting with any of the ads, as there’s no telling, which of them may have been tampered with by third parties and what consequences that may have for you.
Preventing future encounters
Whether this is your first encounter with a browser hijacker or it’s already happened before, you probably might not want to have this happen to you again. For that purpose we have some advice that you may like to follow from now on. As programs like Linenews.org tend to rely on other programs for their distribution, it’s important that you mind your download sources henceforth and also customize the installation process of any new program you wish to incorporate in your system. Use the advanced or custom settings in the installation manager, so that you can opt out of any added components such as browser hijackers or other unwanted programs.
Linenews.org “Virus” Removal
I – Safe mode and revealing hidden files
II – Uninstallation
[bannerMiddle]
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
If you are unable to spot Linenews.org, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
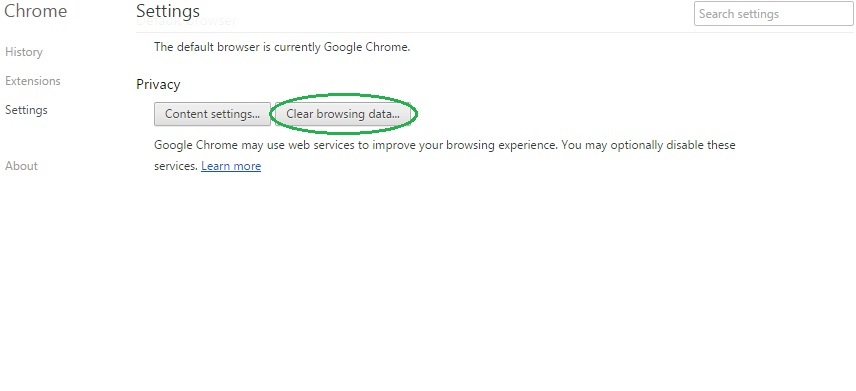
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
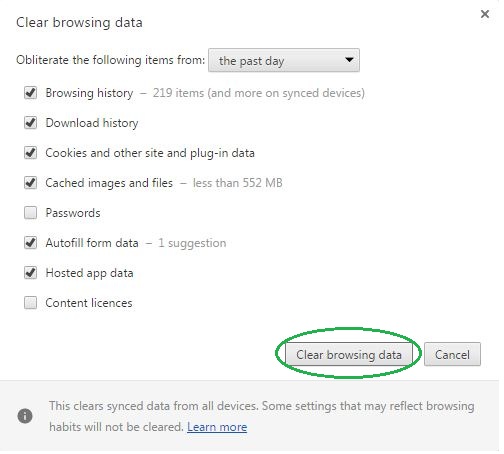
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Linenews.org on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Linenews.org might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Linenews.org, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
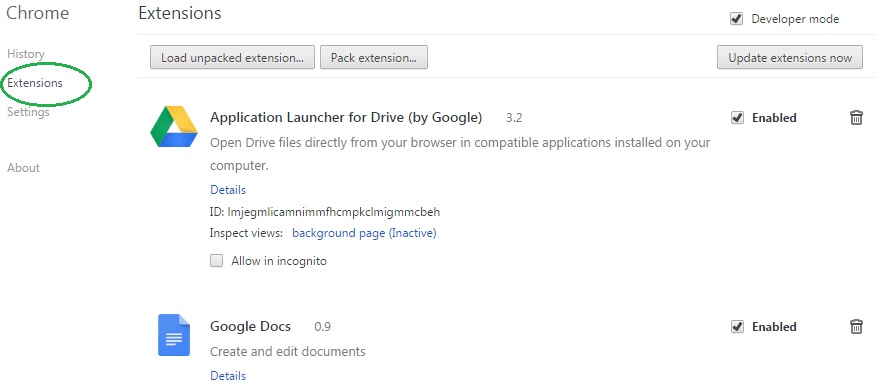
- In the start menu search box write View Network Connections and open the first result.
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
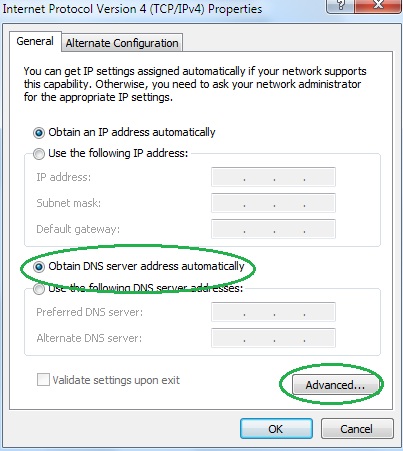
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
