Welcome, reader, to our HowToBleases.xyz “Virus” removal guide. The following instructions will aid you in removing the unwanted software from your PC.
We have created this article with the purpose of letting you know how HowToBleases.xyz (a program described as a browser hijacker) could work. Such software may often provoke changes in the way your browsers look and function. Some annoying generation of ads could start; some redirecting to various websites might begin and the way your browsers (all of them – Mozilla, Chrome and Explorer) look could be changed. Browser hijackers are becoming more and more widely spread nowadays. Generally, the programs from this software family are not known for causing any serious trouble or actual damage to the affected system or its user. However, they could really spoil your browsing experience because of their ability to infect and change the settings of all your browsers. Basically, this is what browser hijackers do: they infect your browsers, produce pop-up and various other types of online ads; redirect you to different promotional pages and other web locations, without necessary asking for your consent; and set a new homepage and a new default search engines.
Are these programs dangerous in any way?
We cannot talk about any ties to any kind of malware here. Browser hijackers are normally considered non-invasive and lacking the ability to damage your computer in a serious way. Indeed, no grave danger could ever come from them. In comparison, if we take a Ransomware-based virus, for instance, or a Trojan-based one, you may end up being unable to access certain files; being harassed for your money or being hacked and spied on by hackers. In the case of the HowToBleases.xyz “Virus”, all these negative consequences are highly improbable.
Still, could HowToBleases.xyz result in something relatively negative?
Of course, every kind of software has its negative traits. In the case of this hijacker as well as any other, by the way, the negative result could be the research that such software could conduct, in an attempt to gain information about your recent search requests and browsing history. Such a practice could be perceived as invasive by some users and is even often seen as a privacy violation. Also, your entire system could become slightly more sluggish due to the high consumption of system resources (because of the redirection and the production of pop-up ads). This type of software normally has only marketing functions. Certain producers pay certain programmers to come up with a piece of software capable of promoting particular products and services in an effective way, and this is how browser hijackers, as well as Adware have emerged. This is business and there is nothing wrong about that.
How does an infection occur? What are the potential sources of HowToBleases.xyz?
The infection with this sort of software can never take place without your direct or indirect permission. These programs are not malicious and they cannot self-install on your PC. As a result, their creators have come up with a way to tempt users into indirectly agreeing to install such programs. The scheme works in the following way:
Hijackers are included in program bundles. These bundles are mostly free and anyone can download them from the web. Usually, people are impatient about using a component of such a bundle – a free app or game, and install the bundles in the quickest possible way. This is wrong because in this way you install the entire bundle on your computer. The way to install only the necessary programs from such a mixture is to always use the Custom or the Advanced installer feature. This will save you from catching annoying programs like hijackers. Remember to stay away from options named ‘Quick / Default/ Automatic or Easy’. This is a general piece of advice and may even prevent you from getting infected with viruses like Ransomware and Trojans.
It is always beneficial to be able to trust a great anti-virus program, so try invest in the best one. Some of the really good anti-malware tools have anti-ad-producing program features and may stop programs like the HowToBleases.xyz “Virus”. Also, just choose the websites you visit very carefully and you will be unlikely to come across malware and hijackers. For the total removal of the HowToBleases.xyz “Virus” from your system, trust a good uninstallation guide like the one we have assembled for you below. The instructions there have been created with great attention to detail and should be the tool to help you remove this irritating program.
SUMMARY:
| Name | HowToBleases.xyz |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Modified browser settings and sometimes a slight slowdown of your machine. |
| Distribution Method | Software bundles, torrents, shareware, contagious web pages. |
HowToBleases.xyz Removal
I – Uninstallation
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot HowToBleases.xyz, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
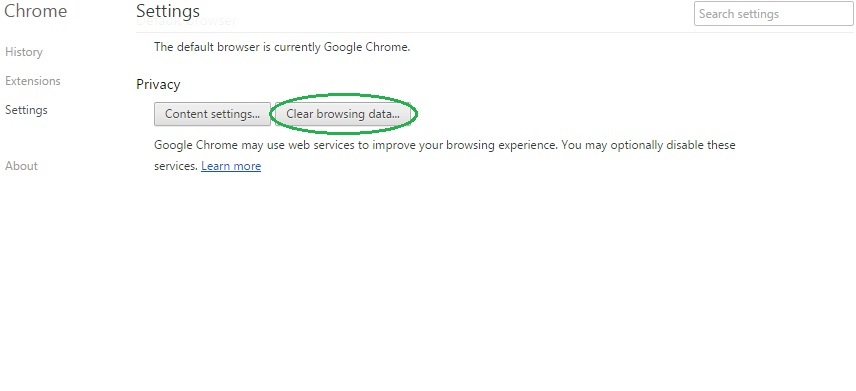
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
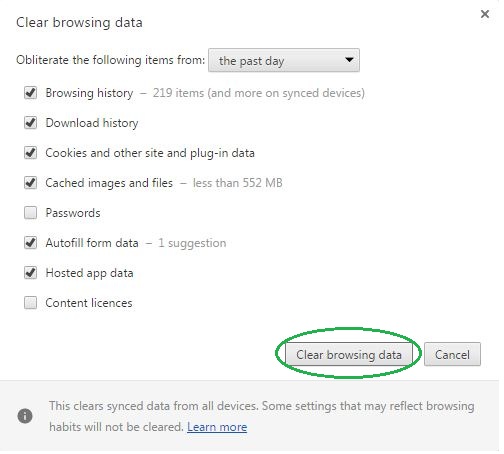
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name HowToBleases.xyz on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name HowToBleases.xyz might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by HowToBleases.xyz, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
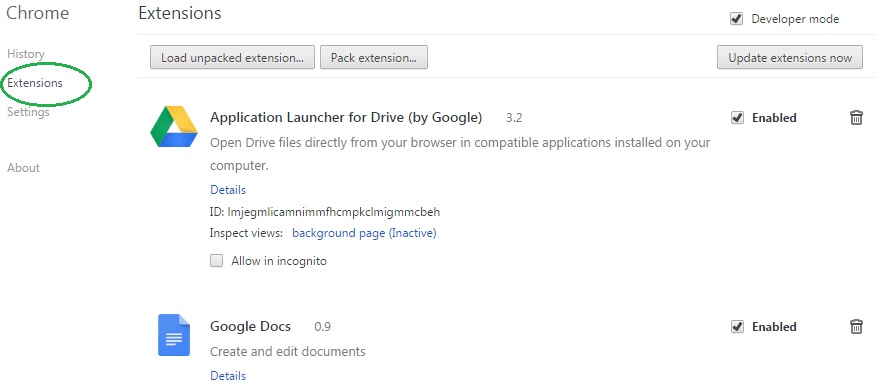
- In the start menu search box write View Network Connections and open the first result.
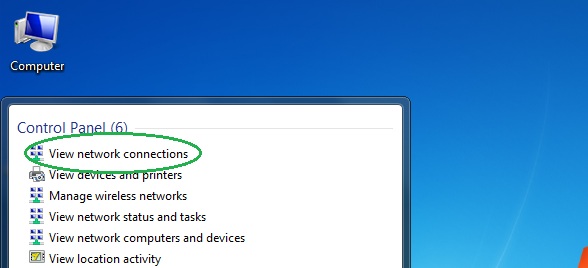
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
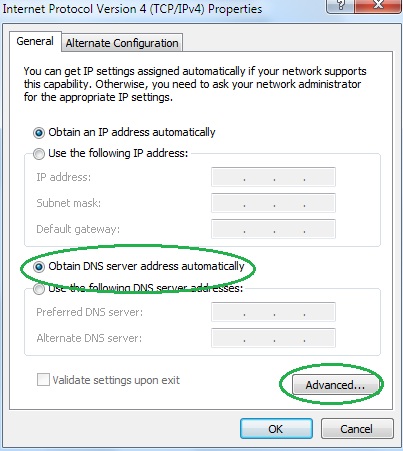
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
