Welcome, reader, to our removal guide, which will help you remove the Yeabd66.cc “Virus” from chrome and all other browsers.
Recently, a program known as Yeabd66.cc has been reported to mess with users’ Firefox, Chrome or IE browsers, changing their homepages, adding unwanted toolbars and search engines and generally making one’s online experience miserable. The aforementioned symptoms are typical for a type of programs called Browser Hijackers. Since you have ended up on this page, you are most likely currently dealing with Yeabd66.cc, which too falls under that category of unwanted and intrusive software. Here, we will do our best to help you solve your current issue as well as improve your knowledge regarding Browser Hijackers, so that you can better avoid them in the future.
Introducing Hijackers
Now, you might be wondering, what is the point of all that annoyance and intrusiveness from these programs. Well, truth be told, most of the time it’s all about the profit they generate for their creators. You see, the majority of Hijackers have a number of built-in features that allow them to earn substantial amounts of income through online marketing. The problem is that this oftentimes includes them heavily obstructing your regular browsing experience. This is why they are usually considered unwanted. At times, it’s possible that some of them might actually contain some sort of useful functionality but even in those cases, it’s still not worth keeping them due to the negative effects that they might have on your system and online activity.
The importance of removing Yeabd66.cc
Before we get any further, it’s important to know that most of these programs are legal. Many people think that Browser Hijackers are some kind of malicious software similar to the infamous Ransomware viruses. This is not true – Yeabd66.cc, though annoying, is generally considered safe and harmless. With that being said, it is still crucial that you uninstall and remove the nagging application as soon as you finish reading. For that purpose, we have a specialized removal guide below the article that will help you remove the Hijacker right away. If you are in doubt whether you should get rid of Yeabd66.cc, here are several more reasons why removal is probably the best course of action:
- Though usually not dangerous themselves, some Hijackers have the tendency to display online banners or pop-ups that might redirect the user to obscure and sketchy websites if clicked upon. Also, fake/exaggerated error messages persuading you to download some PC optimization software are also possible and if present should be avoided.
- Your machine might get severely slowed down due to high consumption of random access memory (RAM) or processor time coming from the Hijacker. Furthermore, your browser might become non-responding and your system might experience freezes due to the annoying program.
- Additionally, some Browser Hijackers have a feature that allows them to look at your browser searches and gather marketing information that is later utilized when adverts are being displayed in your browser. Surely, no one would want to have their online activity monitored by some obscure programs, therefore, we strongly advise that you uninstall Yeabd66.cc ASAP.
PC protection rules and tips
Most users don’t even realize that an unwanted program got installed on their computer until they start seeing the symptoms. This is because Browser Hijacker developers oftentimes try to employ stealth installation when distributing their software. This basically means that the unwanted program is installed without the knowledge of the user. There are quite a few such techniques and here we will cover the most common ones as well as useful tips on how to spot and avoid them.
- Sketchy torrent/file-sharing sites – If you frequently visit and download stuff from such websites, then it is highly likely that this is where the Hijacker came from. That’s why it is very important that from now on you make sure to stick only to sites and pages that are reputable and confirmed as safe, especially if you are about to download something.
- Spam – Everyone hates spam and for a good reason. Not only is it annoying, but also it frequently contains unwanted software and sometimes even viruses. Therefore, if you suspect that an e-mail letter or some other message is some form of spam, avoid it and if possible, delete it from your inbox.
- Bundles – Many programs have additional installs bundled within their setup files. Sometimes those add-ons are useful but know that file-bundling is also one of the most common and effective methods for Yeabd66.cc distribution. Therefore, when installing any new software, make sure to carefully look through its installation menu and see if there’s anything added. If you have the option of a custom installation, opt for that because this is where any bundled applications might be hidden. Once you find out what has been added, uncheck the entries that you think might turn out to be Hijackers or some other form of PUP (potentially unwanted program). Do not continue with the installation unless you’ve done this.
SUMMARY:
| Name | Yeabd66.cc |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Unwanted new toolbars in your browser, changed homepage and search engine and possible intrusive banners and online ads are among the most common indications of a Browser Hijacker installed on your PC. |
| Distribution Method | Most commonly via spam messages, torrent or file-sharing sites, deceptive hyperlinks/browser ads and software bundles. |
How to Remove Yeabd66.cc “Virus”
I – Uninstallation
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot Yeabd66.cc, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
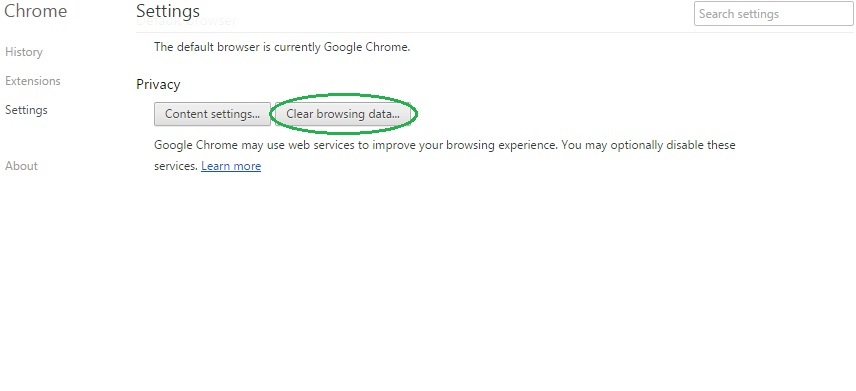
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
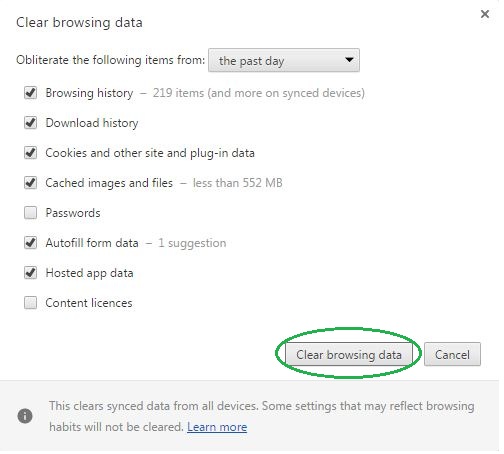
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Yeabd66.cc on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Yeabd66.cc might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Yeabd66.cc, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
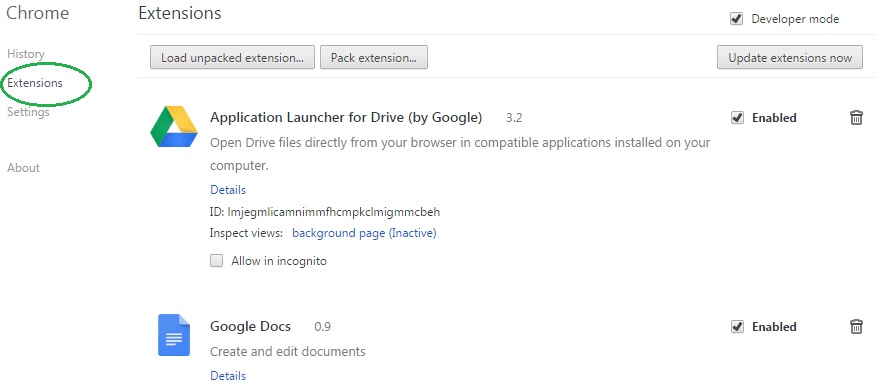
- In the start menu search box write View Network Connections and open the first result.
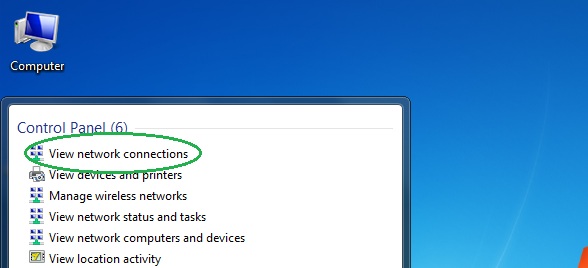
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
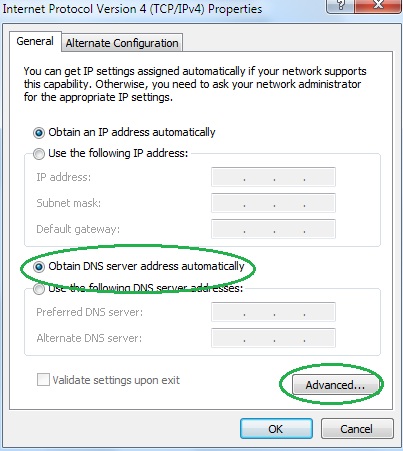
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
