Welcome, reader, to our Web-Start.org how to remove guide. The following instructions will aid you in removing the unwanted software from your PC.
In this article we are going to describe the possible origin of your recent probably unpleasant surfing experience. What you should blame for the constant stream of pop-ups and banners, for the sudden redirect to some strange websites and for the current change in your typical browser homepage and search engine is Web-Start.org. The characteristic features of this program identify it as a browser hijacker. As such, it might affect every single of the popular browsers that you may be using right now: Firefox, Chrome, Opera or Explorer.

What Is Web-Start.org ?
Probably the first question that comes to your mind is whether your computer has been infected with a virus and that is why your browser has been affected so noticeably. However, the news here is good! You are not facing a virus; you are simply experiencing an ad-generating program that may be able to set your search engine to behave differently. Such different behavior of your browser could include the aforementioned changes in terms of produced ads, redirecting to various pages and new homepages. If you had been infected with a malicious program, the consequences for you might have been completely different and so much more terrifying. Probably some of your data would have been encrypted and you would have had to pay to recover it. Probably the infection with an actual virus would have resulted in a complete crash of your PC or the destruction of some files. Here, you shouldn’t worry about such effects as browser hijackers don’t possess any of them.
Why do some specialists consider Web-Start.org potentially unwanted?
There are users who may consider the way this program spreads and the way it functions not quite decent. That has led to the classification of this type of programs as potentially unwanted software products. However, we are going to thoroughly discuss their common features in order to inform you about everything that they may do in detail.
Distribution
Browser hijackers could most often be found inside program bundles. Still, they may be present in email attachments, torrents, shareware websites, pages that stream videos and movies, as well as spam emails. If Web-Start.org has come to you as a component of a bundle, you need to know that these software combinations are legal and programmers create them in order to increase their earnings by being paid for every single advertisement that gets displayed later.
Installation of this hijacker
Maybe it is exactly the methods of installation that make this type of software so questionable. Of course, you probably know that to download a bundle is one thing but to install it on your PC and allow it to integrate itself into your browser is another one. In fact, most of the affected users let this program inside their machines themselves by being quite careless when it comes to the installation features of a given wizard. Web-Start.org typically enters your system and you are completely clueless about that if you tend to select the quick, default or automatic installation features. An important safety tip: learn to use the more time-consuming but apparently nerve-saving installation options if you want to avoid Adware, browser hijackers, Ransomware, Trojans and other harmless or harmful online disturbances. These options are often called advanced or custom.
Other potential negative effects that Web-Start.org might have
In some rarer cases, it might cause some more rather unpleasant things to your system. For instance, the huge production of banners, pop-up and box ads may result in quite the slowdown of your entire machine. Also, some of the redirections that Web-Start.org may be the reason for could lead to places on the web, containing malware (even Ransomware has been mentioned). However, such instances are pretty uncommon, so the irritation and the distraction may be the only negative consequences of having a browser hijacker on your computer that you might experience.
Web-Start.org’s removal: possible or not exactly?
Luckily, as far as we are informed, you are very likely to manage to remove Web-Start.org only by using the removal guide we have assembled for you. Sometimes, under particular circumstances, some more professional advice or help might be necessary. We hope that your case is a simpler one and the guide below will be the tool that can save you from the annoying pop-ups and redirections.
SUMMARY:
| Name | Web-Start.org |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Noticeable changes in the behavior of your search engine: many ads, redirections and an unfamiliar homepage. |
| Distribution Method | Normally, together with other software inside program bundles. |
How to Remove Web-Start.org
I – Uninstallation
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot Web-Start.org, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
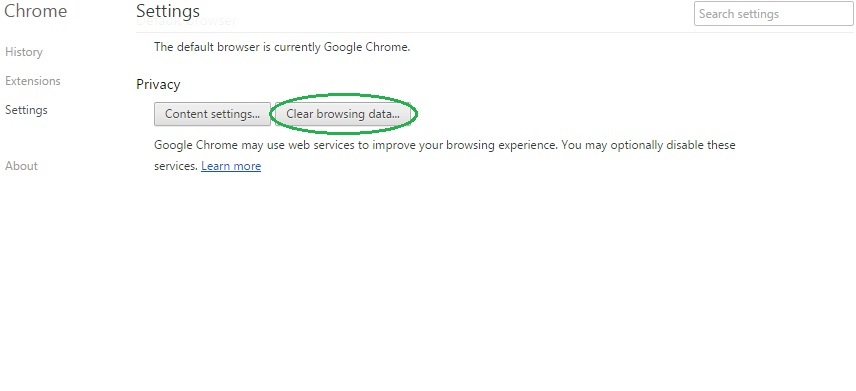
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
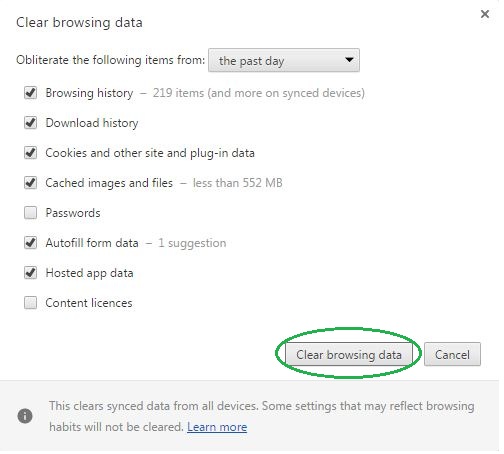
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Web-Start.org on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Web-Start.org might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Web-Start.org, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
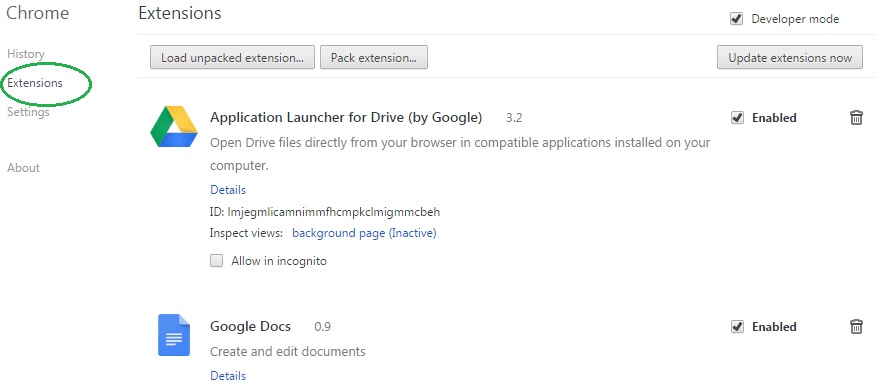
- In the start menu search box write View Network Connections and open the first result.
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
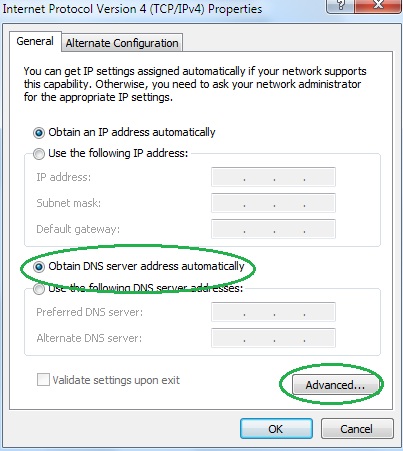
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
