Welcome, reader, to our Findingresult.com “Virus” removal guide. The following instructions will aid you in removing the unwanted software from your PC.
This article represents a brief but detailed description of Findingresult.com “Virus”. Probably you have experienced some of the effects this program could have. Its repertoire might include making your search engines redirect you to unfamiliar places on the Internet while you are trying to browse. Another possible consequence might be the sudden change of the homepage of your default browser, no matter whether you use Chrome, Explorer, Opera or Firefox. In fact, Findingresult.com is a program that may change the settings of any popular browser. Of course, here comes the most irritating feature of this program: the distribution of diverse and numerous online advertisements that may be able to stop you from loading websites or may annoy you greatly with their stubborn popping up without your consent.

What type of a program is Findingresult.com?
Basically, the explanation above covers all the possible effects it may have on your machine. In fact, all of the programs from its family may have such consequences as the aforementioned ones. This is the family of the so-called browser hijackers. You may already be able to guess where their common name comes from – their ability to take control of your search engine and change its settings, no matter which one of the famous browsers you use.
Is that program close to a virus?
Browser hijackers, in general, cannot be compared to any existing malicious software. They are usually not very harmful to your PC, they can only be harmful to your nerves and patience. Let us point out the main differences between hijackers and a typical virus. Most of the malicious programs that have been developed usually have a malevolent purpose. It may be to steal important credentials from your PC. It might be to hijack some data, lock it up and ask for money to recover your access to it (as Ransomware typically does). Another possible purpose of a virus could be to simply crash your computer or turn it into a bot. On the contrary, Findingresult.com and the products from its group don’t come with such evil intentions. Their only purpose is to display as many ads on your monitor and we are going to explain exactly why they do that.
Why do browser hijackers show such big numbers of pop-ups and banners?
Because of the most common reason anyone does anything in the world nowadays – money. The programmers that create and distribute hijackers and Adware are paid by vendors, who want to popularize their products to promote them by generating online ads. Keep calm, as this business practice is completely legitimate and both sides have their benefits from this marketing activity (PPC; pay per click).
How do programmers distribute Findingresult.com?
Another important detail about Findingresult.com that we want to focus about is the way it gets spread. The methods of spreading browser hijackers might be very diverse. They could get distributed via emails (mostly spam but also the ones in your regular Inbox), torrent and shareware-spreading web pages and infected websites. Still, the method that is most regularly used is via software bundling. This process of combining software products results into the creation of program bundles. Inside such a bundle you may find some original programs, some Adware-type products as well as some browser hijackers. Developers mix so many kinds of software because of the money they are promised to get from the pop-ups, banners and the other ads that later get displayed. Also, many developers use bundles to distribute the programs they create themselves for free and still get paid for the ads.
Here comes the most important aspect of the whole infection process: developers can spread Adware and hijackers but they are not able to install them on your PC. Probably your system has ended up contaminated with Findingresult.com because you have installed the whole content of a given bundle yourself. Such an unfortunate event happens with your (unknowing) consent every time you select the inappropriate installation step. The features of your installation wizard are usually two: one that might be marked as Default (Quick/Typical) and the other that might be called Custom (Advanced/ Customized). In order to ensure the health and the safety of your machine, your only reasonable choice is the more detailed option – the Custom one (or however it is called in the given installer). Most of the infected users end up like that because they have chosen the other step and they have unknowingly let the browser hijackers and the Adware from a particular bundle enter their computers.
Is the removal of Findingresult.com possible?
Luckily, you can uninstall Findingresult.com by following the removal instructions of our guide below. They should be enough to save you from this irritating software. However, in certain cases you may need an expert or professional software to help you get rid of this hijacker.
SUMMARY:
| Name | Findingresult.com |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Usually page redirects and annoying ads, as well as altered browser settings. |
| Distribution Method | With program bundles, inside torrents and contaminated web pages. |
Findingresult.com Redirect “Virus” Removal
I – Uninstallation
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot Findingresult.com, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
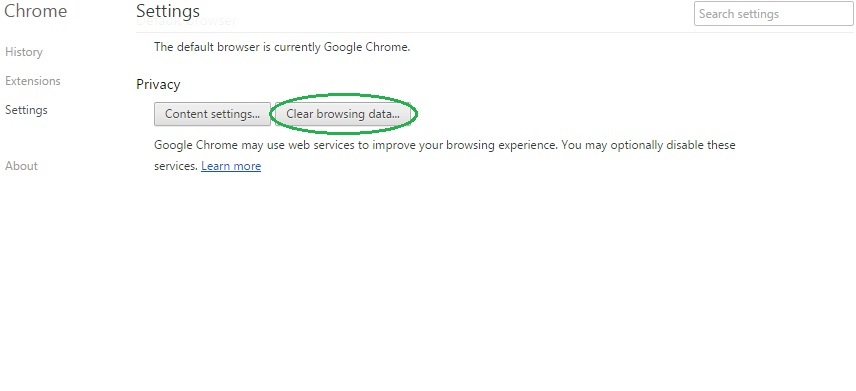
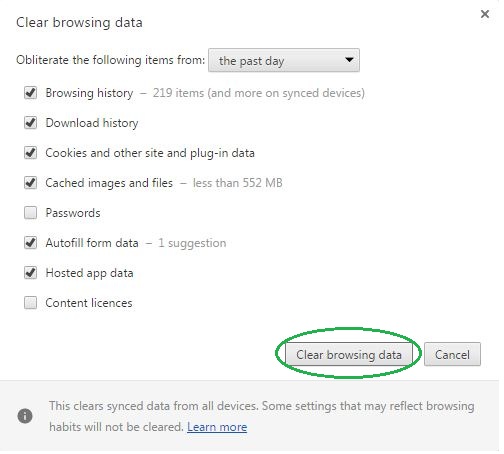
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
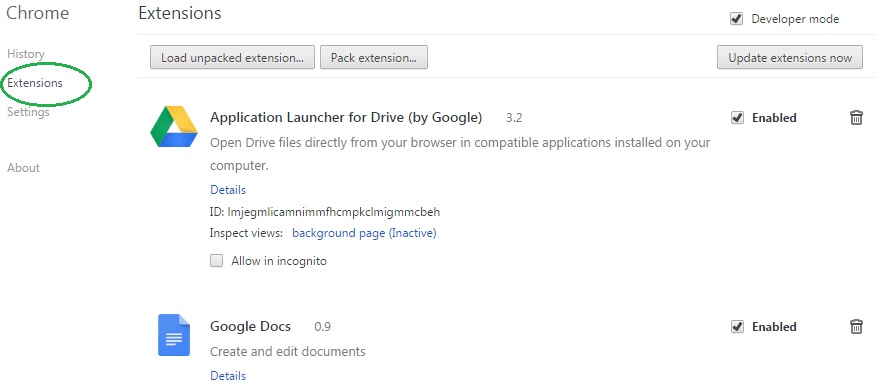
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Findingresult.com on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Findingresult.com might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Findingresult.com, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
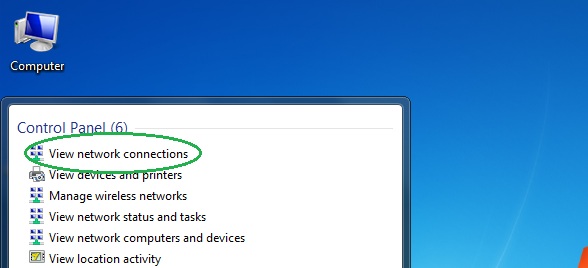
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
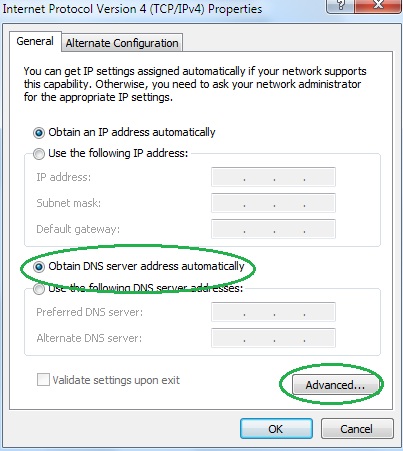
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
