This page aims to help you remove CryptoLuck Ransomware. These CryptoLuck Ransomware removal instructions work for all versions of Windows, including Windows 10.
CryptoLuck – as nasty as it gets
We all know how malicious computer viruses can be – some can spy on you, some can steal money from your online bank accounts and some can outright turn your machine into a useless pile of scrap. There’s just no limit to the potential harms a computer virus can cause, especially now, when most of our work is dependent on our computers. However, did you know that there’s another virus that is unlike any other? Its name is CryptoLuck – Ransomware. CryptoLuck and the other viruses of its type are notorious for locking people’s files and demanding ransom if the user wants to regain access to their own files. Ransomware has been around for quite a while but it was not until fairly recently that this type of viruses has started to become the major threat that it is today. That’s right, Ransomware is currently one of the biggest security hazards that you can encounter online. This article’s goal is to inform you about the most important traits of CryptoLuck and also what possible courses of action you can undertake so as to counteract the malicious program on different stages. We have also included a guide that will show you how to remove the virus from your PC.
How the virus works
As we already said, Ransomware won’t attempt to actually harm your PC, steal your money or anything typical for other types of viruses. Once CryptoLuck infects your system, it replaces all your files with copies of them that are identical. There’s only one difference between the copies and the original files: the copies are all encrypted by a special coding. You would not be able to access any of the encrypted files unless you have a special code. The person who’s created the virus has that code. Once the encryption process is over and all your files have been locked, the virus displays a message that says you need to pay a certain amount of money if you want the needed code. Instructions on how to pay the ransom are also provided in the message. The transfer is usually made via bitcoins – a cyber-currency that is known for being very hard to trace. This enables the hacker to retain their anonymity, without fear of being revealed and brought to justice. This is also one of the reasons why Ransomware viruses are becoming so widely spread. No one is safe from CryptoLuck – cyber-criminals target both regular users and big companies all over the world.
Handling the threat
In this last paragraph of our article, we will give you some invaluable advice on how you can protect your files from getting locked by Ransomware and also what you can do if they have already been encrypted. Keep in mind that prevention is the best option you have. Ransomware viruses are really some of the nastiest and most difficult to deal with once they’re inside your PC, so if you are one of the lucky ones whose computer is still safe and clean, make sure that you keep it that way.
- Tips for prevention
- Good anti-virus software – Ransomware sometimes tends to get into people’s PC with the aid of another virus that serves as a gateway. A reliable security program is a must!
- Avoid shady sites and be careful with your e-mails – these two are the most common methods for distributing Ransomware, so make sure that you’re always vigilant and paying attention to the details.
- Back-up everything important – since Ransomware almost always targets only your files and nothing else, backing them up on a separate device, that has no connection to the internet can greatly reduce the effect of a Ransomware infection. You can use whatever device you want – a portable hard-drive, a flash memory, heck, even an old PC would do the job as long as it isn’t connected anywhere. On the other hand, a cloud might not always be the best option – even though those are quite safe, a cloud might still turn out to be susceptible to ransomware attacks.
- During the encryption process
- There are several indicators of Ransomware that’s currently locking your files. If you manage to notice them before it’s too late, you might be able to intercept and stop the process. Most common symptoms are high CPU and RAM consumption accompanied by less hard-drive free space than your PC’s supposed to have. If you notice any of that, make sure that you shut down your machine and call in a specialist. Also, DO NOT attach any devices to your computer if you think it has been infected by Ransomware – this can only make matters worse, since that other device could get infected as well!
- After your files have been locked
- If it is already too late and your files have been encrypted by CryptoLuck, you have to make a choice between paying the ransom and trying something else. Both ways there’s no guarantee for success. However, we strongly advise against the ransom payment – nothing obliges the hacker to send you the encryption code that you so desperately need. Our advice to you is to try out our ransomware removal guide, below this article. Even though this guide might sometimes not be able to solve all problems caused by a malicious virus of this type, it is a much better alternative to transferring money to a criminal. Besides, there’s a link in the guide to a list of ransomware decryptor tools that gets updated frequently – such tools can get you the code without the need of you to pay anything since such tools are almost always distributed for free.
- If it is already too late and your files have been encrypted by CryptoLuck, you have to make a choice between paying the ransom and trying something else. Both ways there’s no guarantee for success. However, we strongly advise against the ransom payment – nothing obliges the hacker to send you the encryption code that you so desperately need. Our advice to you is to try out our ransomware removal guide, below this article. Even though this guide might sometimes not be able to solve all problems caused by a malicious virus of this type, it is a much better alternative to transferring money to a criminal. Besides, there’s a link in the guide to a list of ransomware decryptor tools that gets updated frequently – such tools can get you the code without the need of you to pay anything since such tools are almost always distributed for free.
CryptoLuck Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
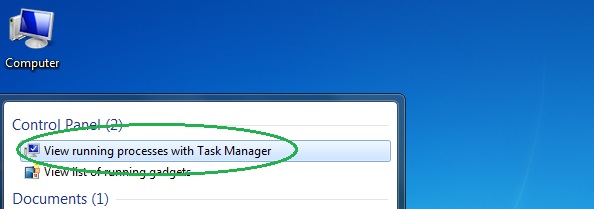
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
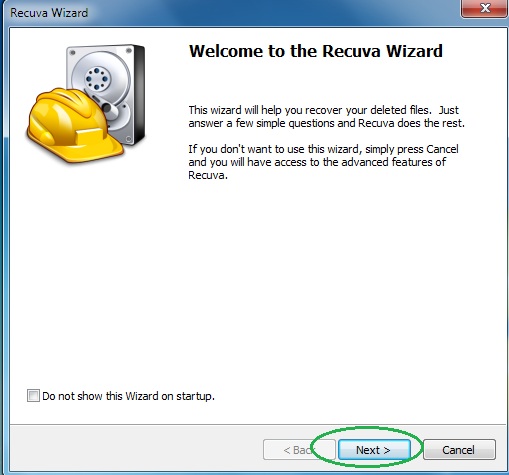
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
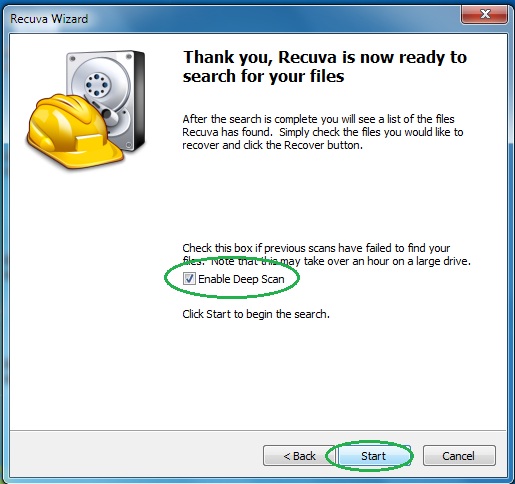
- Wait for the search to finish and then select which of the listed files you want to restore.

