[bannerTop]
Welcome to our Cry128 Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
Ransomware is a type of harmful software that is used for blackmailing purposes. Once a virus of this type infects someone’s computer, it goes on to encrypt the personal files that have been stored on the hard drive of the PC, thus making them inaccessible. Afterwards, a ransom payment is demanded from the victim if they want to regain their access to the locked data.
The Ransomware threat
Today, Ransomware is a global issue and so far no universally effective method for dealing with it has been invented. Furthermore, with each newer version of this nasty malware, it gets more and more difficult to counteract the threat. Here, our focus will be on one newly created Ransomware variant that is known as Cry128 Ransomware. Being well informed as to what these viruses are capable of and how they are getting distributed is crucial if you are to maintain a well-protected and secure machine. We can also offer you a removal guide, which could aid you in removing the infection and decrypt your files in case your PC has already been attacked by Cry128 Ransomware but keep in mind that it is not guaranteed to work in every single case. The effectiveness of the guide heavily depends on the current situation your computer is in. Nevertheless, we believe that paying money to hackers is a really bad idea, thus we advise you not to go for that unless you have tried all other possible methods to resolve the issue.
How does Ransomware work?
There are actually two different types of Ransomware. The less advanced Ransomware viruses do not actually lock your data. Instead, they usually display a screen-wide banner on your PC that cannot be removed and that stays above everything so that you cannot click on anything else but the banner. That way, you would not be able to use your machine unless you get rid of the said banner. If you pay the ransom (instructions on how to do that are within the banner itself) you’d supposedly regain your ability to use your PC. However, here we are focusing on the other Ransomware type – the one that actually locks your files one by one using a sophisticated encryption. Cry128 Ransomware too, falls under that category of crypto-viruses. What’s important to know about this kind of Ransomware is that, since it uses encryption (a file protection technique that is not inherently harmful) it hardly ever get spotted by antivirus programs. The only way that you can potentially spot the threat before it has locked everything is to be very observant of your computer’s behavior so that you can notice even the slightest and subtlest symptom displayed by Cry128 Ransomware.
The symptoms
Do note that those are oftentimes nearly impossible to notice and in some cases the encryption process might happen so quickly that you wouldn’t have any time to take any form of counteraction. Still, knowledge is power and knowledge is what we are trying to give you here.
- Most malware types are known to cause significant increase in the amounts of system resources that are being used on the computer. Therefore, should you notice that there are inexplicably big CPU and RAM spikes in your Task Manager, be sure to go straight to our guide and complete the steps, just in case.
- Next, something very typical about Ransomware viruses is that, apart from RAM and CPU, they also require free HDD space in order to finish the encryption process. If you notice that you have less-than-normal free physical memory on your PC, then there might indeed be Ransomware.
- Last but not least, it is always possible that a virus such as Cry128 Ransomware could make your system unstable, cause errors and even crash your system. This is not that common with Ransomware but it is surely not difficult to notice.
Our advice
There’s no doubt that the best way to deal with a virus of the Ransomware type (or of any other type for that matter) is to simply keep such threats away fro your system. The following list of tips and advice has been designed with the purpose of helping you make your computer better more safe and better protected against hazardous threats such as Cry128 Ransomware.
- Do not go on websites that are obviously not reliable and safe. It is not difficult to notice such sites – they usually have a lot of big and bright banners, cause a lot of redirects and are generally filled with all sorts of intrusive ads.
- Next, go to your browser’s settings and take a look at the Downloads section. If there is some sort of an automatic download function, make sure to disable it. For example, in my browser I have a setting called “Ask where to save each file before downloading” – keeping that enabled would mean that I’ll always be asked if and where I want something to be downloaded instead of the file getting downloaded automatically on my PC.
- Something very important to keep in mind when dealing with Ransomware is to remember to get yourself a backup location. Obviously, this is extremely important and if you don’t have a backup of your valuable files, be sure to make one right away.
- Finally, remember to always have a good antivirus that gets updated at a regular basis. Even if it would fail to spot the Ransomware, it would still increase your PC’s protection against other viruses such as Trojans. Keep in mind that Trojan horses are yet another very commonly used method for spreading Ransomware.
Cry128 Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
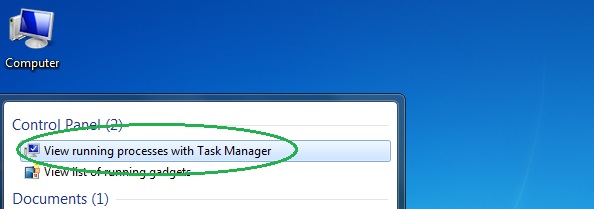
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
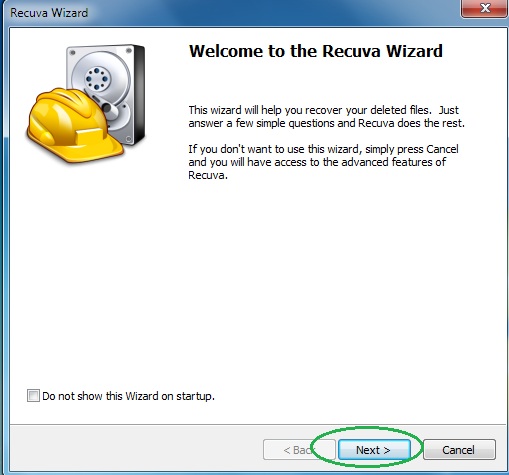
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
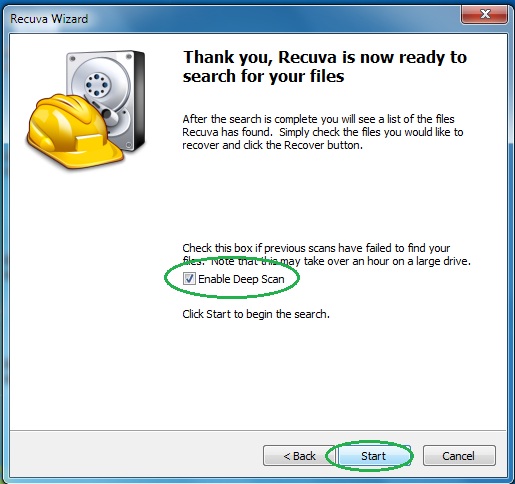
- Wait for the search to finish and then select which of the listed files you want to restore.

