[bannerTop]
Welcome to our Bigpicturepop.com “Virus” removal guide. The following instructions will aid you in removing the unwanted software from your PC.
If you have been infected by a browser hijacker, you know how annoying and what a nuisance it can be. We’re guessing that you are on this page exactly due to such as instance of infection, namely with one of the latest representatives of this software category – Bigpicturepop.com. You probably also determined that an infection has indeed taken place by experiencing the typical for these programs symptoms, which include a change in your browser’s homepage and/ or default search engine. Furthermore, frequent redirects to various sponsored pages may also have raised a red flag, especially if they seem to be occurring for no apparent reason. And it doesn’t even matter which of the most popular browser you may be using, be it Chrome, Firefox, Edge, Opera or some other one – they are all equally susceptible to the influence of browser hijackers and their irritating ads that they may use to fill your screen with. We can very well understand your desire to remove Bigpicturepop.com, if that’s what you’re here for. In fact, that is precisely the reason why we have created the below removal guide, which you may use to remove this browser hijacker from your system and restore you browser settings to their previous state. However, before jumping over to them, we would recommend reading through the following few paragraphs to gain a better understanding of what Bigpicturepop.com is up to on your PC.
What browser hijackers are really up to?
Programs like Bigpicturepop.com serve the online marketing industry – they are, in fact, marketing tools, used to generate and distribute large quantities of online ads, like popups, banners, box messages, in-text links and others directly in the browser of each individual user, who has had the respective hijacker installed on their machine. With all that being said, programs of this type don’t really have any other objective than to promote the various products and services that they constantly display. On the one hand, we have the vendors of these products and services, who benefit from their promotion. But on the other, it’s the browser hijacker developers, who are also directly invested in the successful advertising campaigns. They profit based on remuneration models such as the infamous Pay Per Click scheme. These ensure that every click landed on any of the ads produced by Bigpicturepop.com “Virus” or another hijacker generates a small amount of revenue.
However, there tend to be issues that arise from the developers’ desire to maximize profits and squeeze out as much revenue as they possibly can from the said ads. For one, you’ve noticed that those ads can be fairly aggressive and even prevent you from browsing the web as you normally would, often causing you to lose precious time in trying to close the constantly reappearing new tabs and windows, as well as the obstructive banners. But aside from this tip of the iceberg, there’s also the invisible activity that programs of this type often engage in. We’re talking about the ability of browser hijackers and other programs like Bigpicturepop.com to look through your browsing history and extract certain data from it. Such are the websites you spend the most time on, for example, as well those that you have bookmarked or favourited. In addition, the hijacker may take into consideration the kind of content you tend to like and share on different social media platforms, etc. And last but not least, they also often look into your latest browser search queries. All of this combined can help them determine, which ads you will be more likely to respond to and therefore click on.
However, that’s not the worst of it. In fact, programs like Bigpicturepop.com have the capacity to expose you to threats far worse than this, including Trojan horse viruses, ransomware, spyware and other malware. That’s because hackers and cyber criminals like to inject online ads with viruses, so as to ensure their distribution. Once you click on a malicious ad like that, you are likely to immediately get infected with the virus that was in it. The bad thing is, however, that you won’t be able to distinguish the compromised ads from the legit ones, which is why we would recommend that you try to avoid any online ads and try to steer clear of any.
Bigpicturepop.com “Virus” Removal
I – Safe mode and revealing hidden files
II – Uninstallation
[bannerMiddle]
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
If you are unable to spot Bigpicturepop.com, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
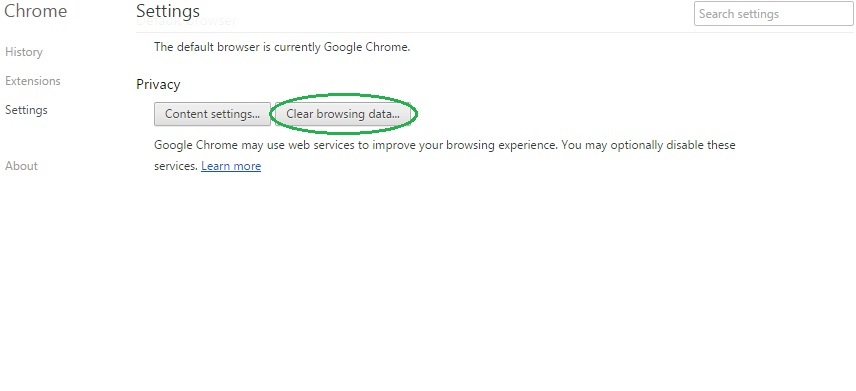
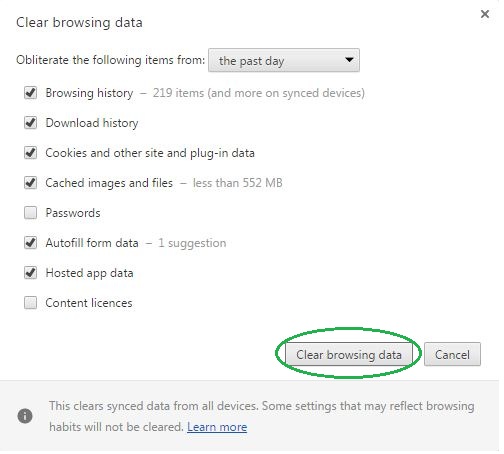
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
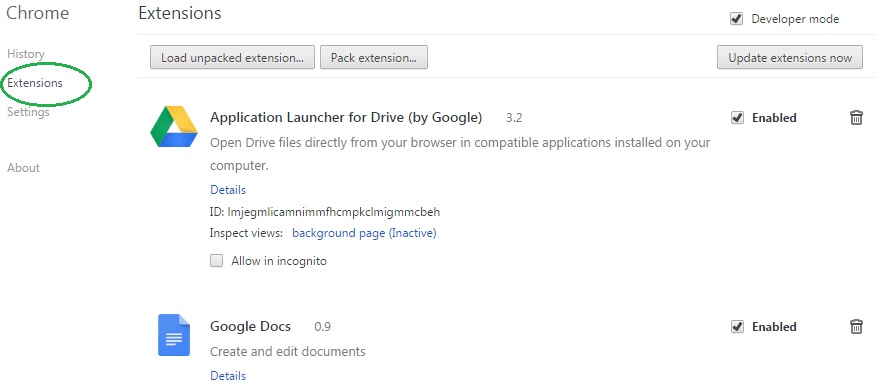
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Bigpicturepop.com on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Bigpicturepop.com might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Bigpicturepop.com, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
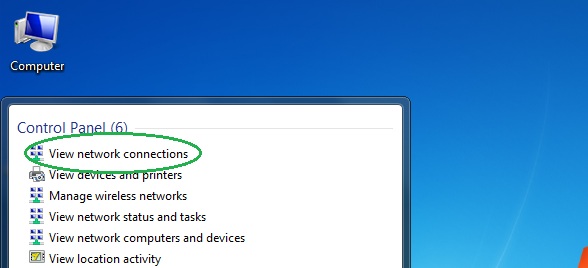
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
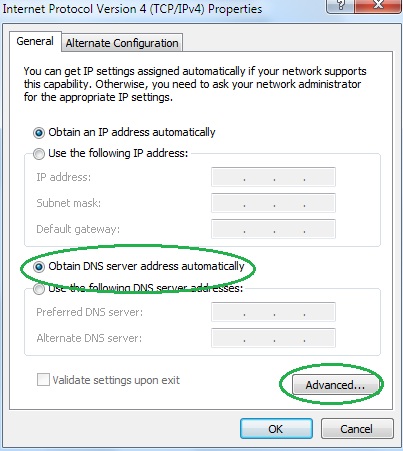
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.
