[bannerTop]
Welcome to our Gdcb removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
In the text that follows, we are going to discuss the details of a new and very harmful Ransomware cryptovirus called Gdcb. This threat has been reported as one of the most horrible computer infections, available on the Internet today. Gdcb Ransomware can secretly sneak inside any computer, infiltrate its files and encrypt them with an almost unbreakable algorithm. Then, the malware will start to blackmail you for the decryption of your data and will ask you to pay ransom. Unfortunately, only one careless click on an infected transmitter can bring about this trouble, that’s why it is extremely important to know how to protect yourself from such nasty Ransomware. The information below contains some very useful tips on that, as well as a Removal Guide and a trusted malware removal tool, which may help you remove the terrifying infection and eventually deal with its consequences, in case that you have been attacked.
Why is Gdcb such a dangerous program?

The file encrypting Ransomware threats are a very complex type of malware. These harmful programs are based on a tricky blackmail scheme. Once they get inside your computer, their job is to take your most frequently used files (work documents, archives, audio and video files, images, etc.) hostage and render them inaccessible with the help of a very complex encryption. The moment you are not able to open or use any of them, a ransom note usually gets displayed on your screen, asking you to pay a certain amount of money (usually in Bitcoins) in order to liberate the affected data. This is a very nasty form of financial and emotional harassment, the aim of which is to extort money from you. You may find yourself being threatened and blackmailed by some anonymous hackers, who may ask any amount of ransom they want and may press you with short deadlines and frightening alerts.
The ways you can catch Ransomware like Gdcb are not any less tricky than the capabilities of the infection. Security experts warn that the most common sources are spam emails from unfamiliar senders, infected attachments, fake ads and pop-ups, misleading links, illegal sites and compromised software installers. Very often, Ransomware can get inside the system with the help of a Trojan horse. The nasty thing here is that you may unknowingly click on the transmitter and this is all it takes for the infection to activate and infiltrate your system. Unfortunately, even if you have an antivirus program (especially an outdated one), it may not always be able to detect and notify you about the Ransomware because the encryption process, initiated by it, is usually not considered as malicious by most of the convenient security products. This means that Gdcb may complete its dirty job and place a ransom notification on your screen absolutely undisturbed and you may not be able to spot it and stop it before it has blocked all of your files.
What is the right way to react if your PC has been infected with Gdcb?
Seeing a threatening ransom message on your screen is surely a shocking experience. All the victims are really concerned not to lose their files forever and oftentimes, in an attempt to release them from the Ransomware encryption, they pay the ransom, required by the hackers. This is a very risky action, which is dictated by fear and frustration, and unfortunately, it does not guarantee the recovery of the encrypted files. If you are thinking about alternatives to save your data and deal with Gdcb, there are some points you should carefully consider.
First of all, Ransomware infections are extremely difficult to deal with. Technically, you may be able to remove the malware with the help of a Removal Guide like the one below. However, your files may not be released from the encryption. Unfortunately, there are not that many methods, which can help you recover them and the only 100% working solution is a full file-backup copy. Paying the ransom is not advisable since you cannot rely on the criminals to send you a decryption solution. Their real goal is to simply get your money and hide their traces while restoring the affected data is surely their last burden. That’s why our advice for you is to look for your own interest and not pay ransom out of fear and frustration. A good way to start is to consult a Ransomware expert, purchase special software to remove the infection, and seek for available free decryptors for your files. The Removal Guide below also contains helpful instructions on how to remove Gdcb and eventually get back some of your data. Even though none of these options can promise you a full recovery, you can still give them a try and check what works best in your case.
Source: Howtoremove.guide’s instructions: Gdcb Ransomware Removal
Gdcb Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
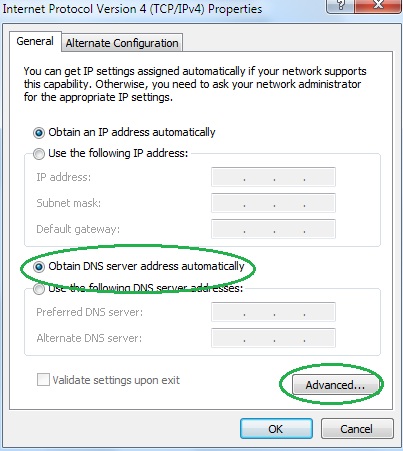
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
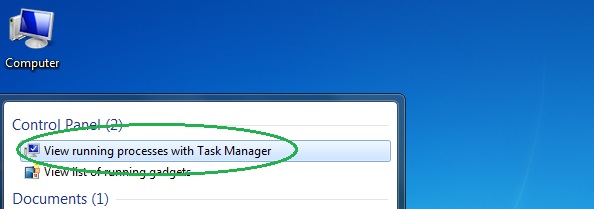
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
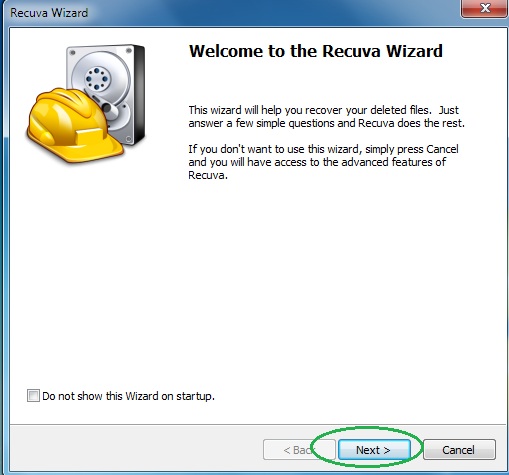
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
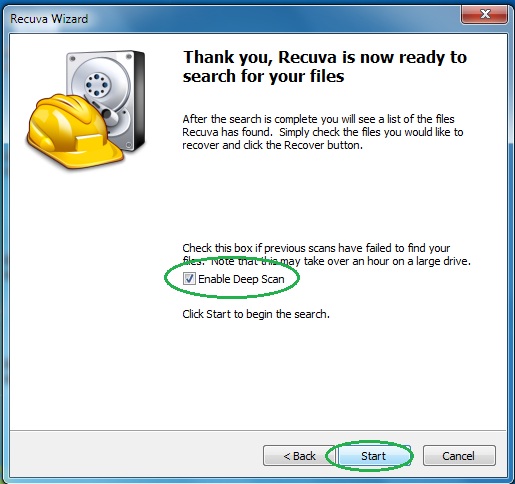
- Wait for the search to finish and then select which of the listed files you want to restore.