[bannerTop]
Welcome to our .Crab Virus Removal removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
In the passages we have prepared for you down below, you can find some important information and facts about .Crab. Also, we are discussing the malicious category this program belongs to – the Ransomware virus category.
To make a long story short, we can say that the viruses from this family including .Crab Ransomware are normally used for locking the user’s data files (or their whole computer) and asking for a ransom payment after the locking-up process has been completed. In the case of .Crab, a complex encryption is used to seal the targeted user files. Another typical characteristic of this sort of malware is the appearance of a scary ransom-demanding message that may really seem frightening. It simply aims to inform you that your data may be lost for good if you don’t agree to pay the amount of money the hackers want from you.
What is Ransomware able to do as a whole?
What could be expected from all Ransomware versions is to lock up something on your device. By sealing certain data we mean rendering it inaccessible to you. Right after the process of encryption has been finished, you will be notified about that by the displayed ransom notification.
In the paragraphs below we will elaborate upon the possible components of your system which could become victims of Ransomware locking. What’s more, we will be talk about the most common forms of this malware and its usual sources. Lastly, we will share some helpful prevention tips and some possible removal instructions to help you resolve your problem with this Ransomware.
How many Ransomware subtypes are there?
There aren’t that many different forms of Ransomware. Here are the two most important and common types that you need to be aware of.
- Ransomware targeting file formats – This subcategory includes all the Ransomware viruses which are programmed to infect your computer and block certain files. Once the malware finds its way into the targeted machine, the encryption process starts and the user’s data files get locked up. The final stage of such a process is usually the generation of a intimidating ransom-requesting alert which serves the purpose of informing you about the malicious activity that has been going on.
- Ransomware targeting the screens/monitors of your devices – This subfamily consists of the Ransomware-based programs used for making you unable to access the desktops of your PCs and the screens of your other devices such as tablets and smartphones. In that case, your files are not truly endangered. Still, you are going to be made unable to access anything on your device because the ransom notification itself prevents you from accessing doing that. Of course, you are going to be asked to pay a certain ransom, however, this time, in exchange for the access to your desktop or screen, not for the access to any valuable files.;
.Crab is basically a part of the file-encrypting Ransomware subgroup. As you already know, this kind of malware is indeed capable of getting to and exploring your device data storages and then targeting certain file formats and later on – encrypt them all.Unfortunately, this is bad news since the file-encrypting viruses are more advanced than the screen-locking ones and oftentimes it is really difficult to deal with such an infection.
Possible sources of .Crab Virus Ransomware:
Everything that is online may be contaminated by Ransomware and be used to spread such viruses. Still, there are some sources that are more frequently used than others:
- Spam e-mails with file attachments: Each of the emails sent to you may carry viruses such as .Crab (or other forms of Ransomware). We suggest that you simply stop opening the ones you have not really expected or the ones which come from unknown senders. Moreover, just stay away from all shady attachments (such as strange .exe files, documents and images).;
- Malicious ads: Malvertising is another really major source of Ransomware. It enables the distribution of pop-ups and other versions of ads that may be able to redirect to potentially infected web pages. That’s the reason why you should avoid interacting with any ads that coming from shady web sources.
- Torrents (the illegal web platforms spreading illegal software): Some of the other more frequent sources are the software, movie and torrent-distributing online platforms which could be illegal and normally violate various copyright policies and laws.
What is the solution to such a problem then?
There is no stated always-working solution against Ransomware and .Crab provided that the infection has already successfully occurred.
However, you are still encouraged to seek alternatives and not just pay the money that the hacker has demanded straight away. The crucial tip is to always avoid paying the wanted ransom before you have run out other possible solutions. A free potential way to handle this virus is our Removal Guide below. Make sure to try it!
.Crab Virus Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
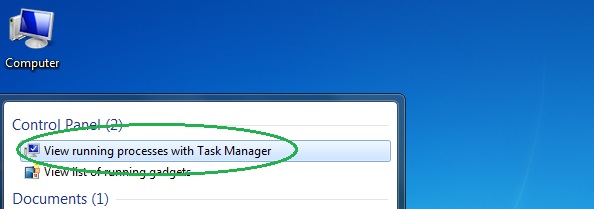
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
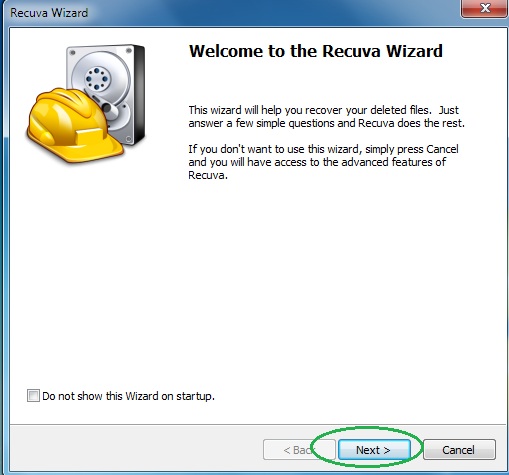
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
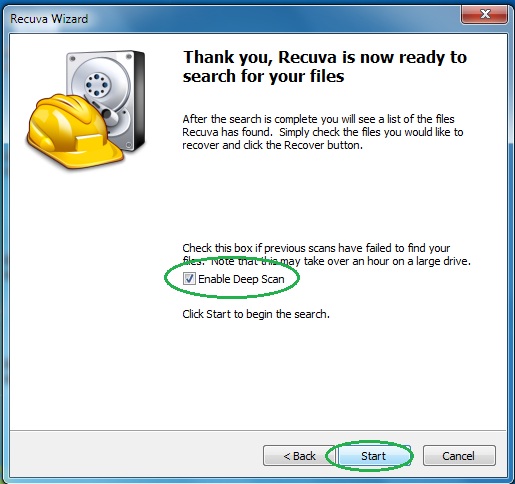
- Wait for the search to finish and then select which of the listed files you want to restore.


You guys have been so great at responding! I was hit with a Ransomware virus that converts your files to something like: apzyalaz.locked and leaves the file, “HOW_TO_DECRYPT_FILES.html I”ve heard it called the LockeR ransomware. I have copies of an encrypted and unencrypted file. Would you be able to help me decrypt it? THANK you in advance for any help or replies!
Currently, there seems to be no available decryptor for this particular Ransomware. Sadly, all you could do is wait until one such tool gets released.